
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Produce the following program.
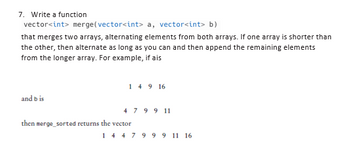
Transcribed Image Text:7. Write a function
vector<int> merge(vector<int> a, vector<int> b)
that merges two arrays, alternating elements from both arrays. If one array is shorter than
the other, then alternate as long as you can and then append the remaining elements
from the longer array. For example, if ais
and bis
149 16
4 7 9 9 11
then merge_sorted returns the vector
1 4 4 7 9 9 9 11 16
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Show output of these programs.arrow_forward(python) 9. Create a function based on the following information: You are given two strings with words separated by commas. Try to find what is common between these strings. The words in the same string don't repeat. Your function should find all of the words that appear in both strings. The result must be represented as a string of words separated by commas in alphabetic order. Input: Two arguments as strings. Output: The common words as a string. Return: Nothing is returnedarrow_forwardplease quickly thanks ! use Pythonarrow_forward
- [Python Language] A common back-of-the-envelope technique for estimating a runner’s marathon time is to take their best half-marathon time, multiply by two and add ten minutes. This works pretty well unless the marathon course is hilly.If it is hilly, we add an extra 20 minutes to the estimate. Write a program that takes two lines of input: a float giving the half- marathon time in minutes and an integer indicating whether the marathon course is hilly(1) or not (0). It prints a float giving the estimated number of minutes the runner will take to run the full marathon. Write your pro- gram in a file named marathon.py.arrow_forwardCould you make sure the code is correct. Please read the instructions carefully and the example runs. Thanks.arrow_forwardhow to write a function that takes an integer n and prints all of the integers between 1 and n which are multiple of 5 using while looparrow_forward
- Describe what the following code is doing (the outcome), by annotating each line of code and giving an overall description of the function of the code. Also, perform a desk check (trace) of the program. Must show multiple iterations of the program loops in the desk check (trace). MOV RO, #100 MOV R1, #2O Loop: CMP RO, R1 BEQ Stop BLT Less SUB RO, RO, R1 BAL Loop Less: SUB R1, R1, RO BAL Loop Stop: MOV R7, #1 SWI Oarrow_forwardPython (this is not graded this is practice work that is not graded) write and test a function which takes two dates (month, day) list arguments.When the function is called with the two arguments, it returns the number of days betweenthose two dates. Print the returned value. It is assumed that the first date occurs first. Forinstance, if the users calls the function with FUNCTION([12, 10], [12, 20]) as arguments, thereturned value is 10 days. However, if FUNCTION([12, 20], [12, 10]) is called, the returnedvalue is -10 days.Assume February has 28 days.Test data: [10, 30], [5, 20] [1, 30], [5, 25] [5, 25], [1, 30] [1, 1], [12, 31]arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education