
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Concept explainers
Question
a) Design an efficient
[Important instruction: Create an arbitrary list of 10 lectures starting times and their corresponding ending times to provide full explanation of how your proposed
algorithm should work step by step]
b) Implement your efficient algorithm using Python
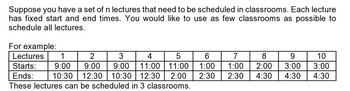
Transcribed Image Text:Suppose you have a set of n lectures that need to be scheduled in classrooms. Each lecture
has fixed start and end times. You would like to use as few classrooms as possible to
schedule all lectures.
For example:
Lectures 1
2
3
4
5
9:00 11:00 11:00
Starts: 9:00 9:00
Ends:
2:00
10:30 12:30 10:30 12:30
These lectures can be scheduled in 3 classrooms.
6
1:00
2:30
7
8
1:00 2:00
2:30
9
10
3:00 3:00
4:30 4:30 4:30
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 5 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- pythonarrow_forwardC++ I really need help with Question #6 A,b, and c. please I would really appreciate it.arrow_forward(a) Devise a recursive algorithm using design by induction for computing n2 where the input to the algorithm n is a nonnegative integer. Use the fact that (n + 1)2 = n2 + 2n + 1. (b) Discuss the running time requirements of your algorithm.arrow_forward
- The following equation can be used to compute values of y as a function of x: y=be¯ªsin(bx) (0.0012x¹ −0.15x³ +0.075x² +2.5x) where a and b are parameters. (a) Write Python code to compute a vector y for a = 2, b = 5, and x as a vector with values from 0 to π/2 in increments Ax= π/40. (b) Compute the vector z = y² with element-by-element-wise operations. (c) Combine x, y, and zinto a 3-column matrix W.(Hint use np. hstack function) (d) Generate a plot of y and z versus x. Include a title, axis labels, and a legend. For the y versus x curve, format a solid blue line. For the z versus x curve, choose a magenta dashed line. Include grid lines.arrow_forwardExercise 3. For each of the following program fragments give a (.) estimation of the running time as a function of n. (a) sum = 0; (b) (c) (d) (e) for (int i = 0; i< n * n; i++) { for(int j = 0; j < n/2; j++) sum++; } sum = 0; for (int i sum++; +; } for (int j } sum = for = } = 0; j < n/2; j++) { sum++; } 0; (int i = 0; i< n * n; i++) { for (int j = 0; j < n * n; j++) sum++ sum = 0; for (int i = 0; iarrow_forwardFor each problem, please provide i. Describe the worst-case input (the input that would cause the largest running time) Summation used to calculate number of steps for the worst case Explanation of how the code relates to the summation ii. iii. a. (loops require discussing number of iterations and steps per iteration) b. (recursion requires a diagram) A O bound iv.arrow_forward
- The following equation can be used to compute values of y as a function of x: y=be¯ªsin(bx) (0.0012x¹ −0.15x³ +0.075x² +2.5x) where a and b are parameters. (a) Write Python code to compute a vector y for a = 2, b = 5, and x as a vector with values from 0 to π/2 in increments Ax= π/40. (b) Compute the vector z = y² with element-by-element-wise operations. (c) Combine x, y, and zinto a 3-column matrix W.(Hint use np. hstack function) (d) Generate a plot of y and z versus x. Include a title, axis labels, and a legend. For the y versus x curve, format a solid blue line. For the z versus x curve, choose a magenta dashed line. Include grid lines.arrow_forward2. R(N) is the running time of strange_sum when called on a List of length N. Since this is recursive code, your answer to iii should include a diagram of the recursion tree. a. Answer for li being an ArrayList b. Answer for li being a LinkedList static int strange_sum(List li) { return strange_sum_helper(li, 0, li.size() - 1); static int strange_sum_helper (List arr, int left, int right) { if (right - left < 0) return 0; else if (right else { int mid = (left + right) / 2; return strange_sum_helper(arr, left, mid) left 0) return arr.get(left); == + strange_sum_helper(arr, mid + 1, right); } }arrow_forwardPlease do it in pythonarrow_forward
- ii.Building on your decomposition for part c.i., develop an algorithm for solving the problem. Include this algorithm in your solution document, and also write down your PI and the individual number that you have obtained via Steps 1–3 from your PI H5737055arrow_forward3. Write a C++ program that implements the following three algorithms and times for various values of n. The program should display a table of the run times of each algorithm for various values of n. //Algorithm C sum = n * (n + 1) / 2 //Algorithm A sum = 0; for (i = 1 to n) sum = sum + 1 //Algorithm B sum = 0; 1 to n) for (i { for (j = 1 to i) sum = sum + 1 }arrow_forwardExpress the Euclidean Algorithm in pseudo-code, then convert your pseudocode to a Python Program. "The Euclidean algorithm finds the greatest common divisor of two positive integers X and Y by the following process: As long as the value of neither X nor Y is zero, assign the larger the remainder of dividing the larger by the smaller. The greatest common divisor, if it exists, will be the remaining non-zero value."arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education