
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Create a program in Java, the chars array stores 100 characteres, and the counts array stores 26 counts, each of which counts the occurrence of letter.
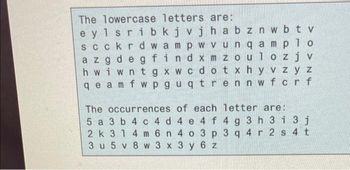
Transcribed Image Text:The lowercase letters are:
eylsrib kjvjhabznwbtv
scckrdwampwvunq amplo
az gdeg findxm zoulozj v
hwiwntgxwcdotx hyvzy z
qe am fwpguqtrennwfcrf
The occurrences of each letter are:
5 a 3 b4 c4 d 4 e 4 f 4 g 3 h 3 i 3 j
2 k 31 4 m 6 n 4 o 3 p 3 q 4 r 2 s 4 t
3 u 5 v 8 w 3 x 3 y 6 z
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Write a C# program that initializes 100 values in array and prints all the multiples of 78.arrow_forwardA single array can contain information of different data types (integers, characters, decimals, and so on). a. True b. Falsearrow_forwardCreate an array and store 10 multiples of 5 and print it out. Use for loop to generate the multiples and then print them out using a second for loop. 5 10 15 20 25 30 35 40 45 50 Note: You cannot get any credit if you don't use array or for loop. JAVA CODE class Main {public static void main(String[] args) {}}arrow_forward
- In C language, write a program which creates an array of N elements of type integers. Output and display how many elements are both multiple of 2 and multiple of 5. example, when the input value of N is 5. input result 5 10 20 5 4 3 2arrow_forwardThis is need in Java Declare an array named temperatures that can hold 10 doubles.arrow_forwardIn C Programming Write a main function that declares an array of 100 ints. Fill the array with random values between 1 and 100. Calculate the average of the values in the array. Output the average.arrow_forward
- programming used: javaarrow_forwardCODE IN JAVA design a program that grades arithmetic quizzes as follows: (Use the below startup code for Quizzes.java and provide code as indicated by the comments) 1. Ask the user how many questions are in the quiz. 2. Use a for loop to load the array. Ask the user to enter the key (that is, the correct answers). There should be one answer for each question in the quiz, and each answer should be an integer. They can be entered on a single line, e.g., 34, 7, 13, 100, 8 might be the key for a 5-question quiz. You will need to store the key in an array called "key". 3. Ask the user to enter the student's answers for the quiz to be graded. There needs to be one answer for each question. Note that each answer can simply be compared to the key as it is entered. If the answer is correct, add 1 to a correct answer counter. need this in a separate for loop from the loop used to load the array. 4. When the user has entered all of the answers to be graded, print the number correct…arrow_forwardIn C write a grading program as follows.- Ask the user for the number of students and store it in an integer variable.- Create an array of floats with four rows and columns equal to the number of students storedearlier.- Initialize the array to zeros.Create a menu with the following options (use a do-while loop and repeatedly display the menu):A or a to add student info one student at a timeT or t to display class average for homeworkS or s to display class average for quizzesB or b to display class average for examsZ or z to exit program (program repeats until this exit command is entered)arrow_forward
- Code with comments and output screenshot is must. Thank you!arrow_forwardWrite a program in C as follows:- Create an array of integers named “toy” that has 120 rows and 4 columns.- The program should repeatedly display the following menu:A or a to add a toy to the bagV or v to calculate and display the total value of the toysW or w to calculate and display the total weight of the toysD or d to delete a toy from the arrayM or m to calculate and display the number of small toysN or n to calculate and display the number of medium toysL or l to calculate and display the number of large toysX or x to start filling a new bagP or p to exit program - Santa’s bag can hold 30 large toys or 60 medium toys or 120 small toys or any combination ofsizes that satisfy this requirement (ex: 29 large + 1 medium + 2 small would be max capacity).Also, the total weight of toys cannot exceed 620 Kgs. All values are entered in centimeters andgrams. (Hint: the return values of the size function should help you in calculating the bagcapacity.)The…arrow_forwardDesign a program that asks the user to enter a store’s sales for each day of a 7 day week. The amounts should be stored in an array. Use a loop to calculate the total sales for the week, the average sales per day, and also display the list of values. This is for java.arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education