
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
create a simple code in python for the pseudocode videogame flowchart below
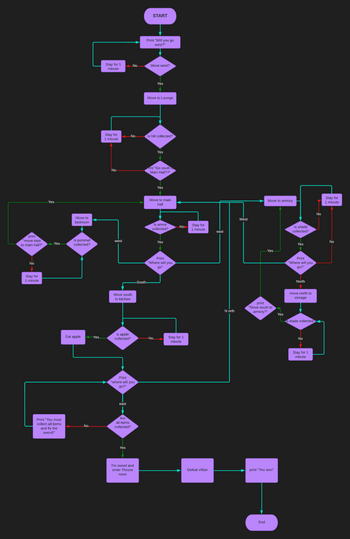
Transcribed Image Text:print
"move east
to main hall?"
No
Stay for
1 minute
Yes
Yes
Print "You must
collect all items
and fix the
sword!"
Move to
bedroom
is pommel
collected?
Eat apple
No
Yes
Stay for 1
minute
Stay for
1 minute
No
west
Move south
to kitchen
is apple
collected?
east
Print
"where will you
go?"
No
Are
all items
collected?
Yes
No
room
Fix sword and
enter Throne
START
Print "Will you go
west?"
Move west?
Move to Lounge
-South-
Yes
Is hilt collected?
Print "Go south
Main Hall??"
Yes
Yes
Move to main
hall
No
Is armor
collected?
Yes
Print
"Where will you
go"
No
Stay for 1
minute
Stay for
1 minute
Defeat villian
east
N orth
West
Move to armory
Yes
print
"Move south to
armory?"
End
print "You won"
Yes
Is shield
collected?
Yes
Print
"Where will you
go?"
North
move north to
storage
is blade collected?
No
Stay for 1
minute
No
Stay for
1 minute
No
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Write in python please Write a nested for-loop to create the pattern below. (Hint: image is 8 x 20).arrow_forwardWhat type of statement takes you to the next iteration of a loop in Python?arrow_forwardWrite a python program that uses nested loops to display a pattern like the examples below. It must not use any formatting operators (e.g., string concatenation) to print the strings to the terminal. Example pyramid ./ ...// ...../// .......//// ........./////arrow_forward
- Loops in Python have blocks that are delimited by: O8 braces () brackets Indents All of the abovearrow_forwardCreate a flowchart and a java program using while/do-while that accepts as input an integer value N (assume N > 1) and prints out the Ulam sequence that begins with the input value N. Required: The .java file (FamilyName_Ulam.java) containing the code, the flowchart; 2 output image files (Sample1 and Sample2);arrow_forwardWrite a C# program if for example, the input: 9 9 2040 prints the date September 9, 2040.arrow_forward
- What is the intuition behind using a loop statement? What do you gain from using loops in your code? How do you think loops in Python provide code reusability?arrow_forwardpython - Recap: X is an array from -3pi to 8pi in 1000 steps. Write the python syntax for looping over all values of X and updating the value current to -999. where X is an even multiple of pi. Hint, use a for loop and appropriate if statements.arrow_forwardPlease check the question in the image and show full code and output.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education