
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Concept explainers
Question
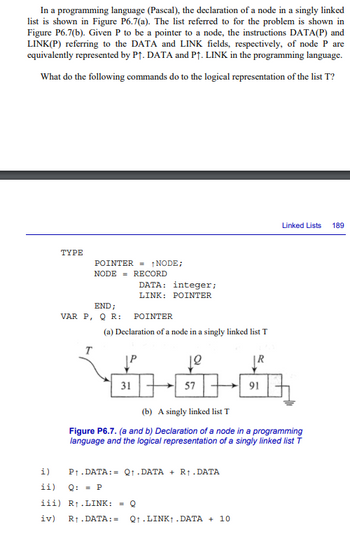
Transcribed Image Text:In a programming language (Pascal), the declaration of a node in a singly linked
list is shown in Figure P6.7(a). The list referred to for the problem is shown in
Figure P6.7(b). Given P to be a pointer to a node, the instructions DATA(P) and
LINK(P) referring to the DATA and LINK fields, respectively, of node P are
equivalently represented by P↑. DATA and P↑. LINK in the programming language.
What do the following commands do to the logical representation of the list T?
i)
ii)
TYPE
POINTER=NODE;
NODE RECORD
DATA:
integer;
LINK: POINTER
END;
VAR P, Q R:
T
POINTER
(a) Declaration of a node in a singly linked list T
31
TE
57
12
(b) A singly linked list T
iii) R₁.LINK: = Q
iv) R₁.DATA: =
P₁.DATA: Q₁.DATA + R₁.DATA
Q: = P
|R
Figure P6.7. (a and b) Declaration of a node in a programming
language and the logical representation of a singly linked list T
Q.LINK.DATA + 10
91
Linked Lists
189
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Consider the following program written in C syntax: void fun (int first, int second) { first += first; second += second; } void main() { int list[2] = {1, 3}; fun(list[0], list[1]); } For each of the following parameter-passing methods, what are the values of the list array after execution? Passed by value Passed by reference Passed by value-resultarrow_forwardWrite a C++ program that: (1) defines and implements a hash class that constructs a 15 element array (may be implemented using a vector, a deque, or a list, if you prefer), storing strings, using the following hash function: ((first_letter) + (second_letter) + (last_letter))% 15 (2) the driver program should: a. query the user for ten words and store them using the hash technique described above. b. print out the contents of each position of the array (or vector, deque, or whatever you used), showing vacant as well as filled positions. Remember, only 10 of the 15 positions will be filled. c. repeatedly query the user for a target word, hash the word, check for its inclusion in the list of stored words, and report the result. Continue doing this task until the user signals to stop (establish a sentinel condition).arrow_forwardDesign and implement a class representing a circular sorted linked list. The class must have the following requirements: The linked list and the nodes must be implemented as C++ templates First must point to the largest value in the list It must include a constructor, a destructor, a copy constructor and an operator= It must include functions to insert a given item, delete a given item, search for a given item, check if the list is empty, return the length of the list and print the list (from smallest to largest) Hint: Use the menu-driven program of the linked list to test all the functions in your class.arrow_forward
- Your task for this assignment is to implement a stack data structure in C++. This may be accomplished by utilizing the C++ standard template library (STL) or by utilizing a user-defined class. 1. 2. 3. 4. Implement a stack data structure using C++. The program will be interactive. Data transactions will be entered as a batch of transactions in a text file at the command line using redirection. The result of each transaction will be displayed on the console. For example: $ prog3 < prog3.dat Each input transaction will contain an arithmetic expression in post-fix format. Assume that each operand and operation (+,-, *, /, %, ^) is a single character in each arithmetic expression without spacing. You may assume that each arithmetic expression is correctly formatted. However, your program should not attempt the following: a. Divide by zero with / or % ... Instead, your program should display an error message and then begin evaluating a new input transaction. b. Perform % with non-integer…arrow_forwardWrite a C code that will search an int type target from a dynamic linked list. The linked list contains int type values inside each of the nodes. The “search” function will use following input-output arguments,Input: Pointer to the head of the list that you are searching Target value that you are searchingOutput: Pointer to the node that contains the target if found or, NULL if not found.arrow_forwardImplement a class representing a circular sorted linked list. The class must have the following requirements: The linked list and the nodes must be implemented as C++ templates First must point to the largest value in the list It must include a constructor, a destructor, a copy constructor and an operator= It must include functions to insert a given item, delete a given item, search for a given item, check if the list is empty, return the length of the list and print the list (from smallest to largest) Hint: Use the menu-driven program of the linked list to test all the functions in your class. Screenshot the output and make comments on each area on the program.arrow_forward
- Each function has local memory associated with it to hold incoming parameters, local variables, and (in some cases) temporary variables. This region of memory is called a stack frame. Question 7 options: True Falsearrow_forwardYou will create two programs. The first one will use the data structure Stack and the other program will use the data structure Queue. Keep in mind that you should already know from your video and free textbook that Java uses a LinkedList integration for Queue. Stack Program Create a deck of cards using an array (Array size 15). Each card is an object. So you will have to create a Card class that has a value (1 - 10, Jack, Queen, King, Ace) and suit (clubs, diamonds, heart, spade). You will create a stack and randomly pick a card from the deck to put be pushed onto the stack. You will repeat this 5 times. Then you will take cards off the top of the stack (pop) and reveal the values of the cards in the output. As a challenge, you may have the user guess the value and suit of the card at the bottom of the stack. Queue Program There is a new concert coming to town. This concert is popular and has a long line. The line uses the data structure Queue. The people in the line are objects…arrow_forwardJAVA PROGRAMMING Arrays are useful to process lists. A top-level domain (TLD) name is the last part of an Internet domain name like .com in example.com. A core generic top-level domain (core gTLD) is a TLD that is either .com, .net, .org, or .info. A restricted top-level domain is a TLD that is either .biz, .name, or .pro. A second-level domain is a single name that precedes a TLD as in apple in apple.com. The following program repeatedly prompts for a domain name, and indicates whether that domain name consists of a second-level domain followed by a core gTLD. Valid core gTLD's are stored in an array. For this program, a valid domain name must contain only one period, such as apple.com, but not support.apple.com. The program ends when the user presses just the Enter key in response to a prompt. 1-Run the program and enter domain names to validate. 2-Extend the program to also recognize restricted TLDs using an array, and statements to validate against that array. The program should…arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education