
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
I need help fixing this python code to output the given inputs described in the image below
:
letter = input()
phrase = input()
count = 0
for i in phrase:
if i == letter:
count = count + 1;
if count != 1:
print(str(count) + " " + letter + "'s")
else:
print(str(count) + " " + letter )
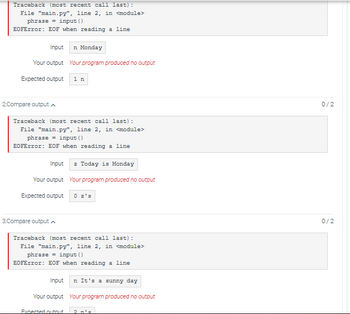
Transcribed Image Text:Traceback (most recent call last):
File "main.py", line 2, in <module>
phrase
input ()
EOFError: EOF when reading a line
Input
Your output
Expected output
2:Compare output
n Monday
Your program produced no output
Traceback (most recent call last):
File "main.py", line 2, in <module>
phrase = input ()
EOFError: EOF when reading a line
3:Compare output
1 n
Input z Today is Monday
Your output Your program produced no output
Expected output
Traceback (most recent call last):
File "main.py", line 2, in <module>
phrase = input ()
EOFError: EOF when reading a line
Expected output
Input n It's a sunny day
Your output Your program produced no output
0/2
0/2
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- I need help with this python computer science DEEP BREADTH SEARCH question. I have the layout of the code but I need help filling in the parts that say "pass" and I want you to take a picture of your output and make sure it matches the sample run below. Find a path (not the best path, but just any path) from A to Z. You see that the green path is not the shortest but it does let us navigate from start to finish. (The picture below) First, we need to know A and Z, our starting and ending points. We'll pass these into our function. I'm going to use a dictionary to represent this graph. Each node (vertex, circle) will have a name, in this case "A" and "Z" were the names of the nodes, but in the generated maps I'm going to use "Node 1", "Node 2", "Node 3", etc. Here is an example web_map web_map = { 'Node 1': ['Node 3', 'Node 2'], 'Node 2': ['Node 1', 'Node 4'], 'Node 3': ['Node 1'], 'Node 4': ['Node 2'] } Node 1 is connected to 2 and 3 for instance, and then also note that…arrow_forwardCan this python code be done without using the isdigit() function. Please try to change the following code in the picture so it doesn't use isdigit().arrow_forwardWrite a program that takes in four positive integers and outputs the number of odd numbers. (Hint: use the modulo operator to determine if a number is odd) Ex: If the input is: 1 2 3 4 the output is: 2 Below is my code so far and I'm getting back unexpected EOF while parsing. I can't figure out what I'm doing wrong. odd_number=[]number_1=int(input())number_2=int(input())number_3=int(input())number_4=int(input())if number_1%2!=0: odd_number.append(number_1)else: passif number_2%2!=0: odd_number.append(number_2)else: passif number_3%2!=0: odd_number.append(number_3)else: passif number_4%2!=0: odd_number.append(number_4)else: passprint(len(odd_number)arrow_forward
- Write a JAVASCRIPT code to repeat the given string to n times and add to it the original string without using loops concat, + operator. for example:- n = 4 given string:- Programmer Output:- ProgrammerProgrammerProgrammerProgrammerarrow_forwardI am having an issue with this program, I keep getting the number 15 everytime I type in a code. There is also the instructions for the module itself. //PSEUDOCODE //Write a program that prompts the user for a binary number //(from 3 to 8 bits) as a String and converts it to base-10 decimal value //There are several ways to do this in Java but your program must use a for loop and first principles to perform the conversion //Print the base-10 number when the loop ends public static void main(String args[]) { long sum = 0; System.out.println("Enter a binary number: "); Scanner scan = new Scanner(System.in); String s = scan.next(); long result = 0; for (int i = 0; i < s.length(); i++) { result = (long) (result + (s.charAt(1) - '0') * Math.pow(2, s.length()- i - 1)); scan.close(); } System.out.println(result); }}arrow_forwardIn Java: Forms often allow a user to enter an integer. Write a program that takes in a string representing an integer as input, and outputs yes if every character is a digit 0-9. Ex: If the input is: 1995 the output is: yes Ex: If the input is: 42,000 or 1995! the output is: no Hint: Use a loop and the Character.isDigit() function.arrow_forward
- can you please show me the code i would use in python spyderarrow_forwardJAVA Write a java program that takes a string as input from the user and finds out if the string is a palindrome or not. A string is a palindrome if it reads the same from forward as well as from backward. For example, the string “madam” is a palindrome. Use a for loop to solve this problem. Sample inputs and outputs: Input: madam Output: palindrome Input: Dad Output: palindrome Input: hello Output: not a palindromearrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education