
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Please write the code in Java eclipse using the UML diagram attached. Add comments.
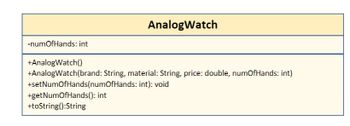
Transcribed Image Text:-numOfHands: int
AnalogWatch
+AnalogWatch()
+AnalogWatch(brand: String, material: String, price: double, numOfHands: int)
+setNumOfHands(numOfHands: int): void
+get NumOfHands(): int
+toString():String
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- we are going to create a new subclass of the SimpleGeometricObject class, namedTriangle. Copy the source code of the SimpleGeometricObject class from the following link: https://liveexample.pearsoncmg.com/html/SimpleGeometricObject.html TASK 1: Create a Triangle class that extends the SimpleGeometricObject class in Eclipse, followingthe below UML diagram. Use the following formula to calculate the area of a triangle: A = 1/2 × base × height TASK 2: Create a TestTriangle class in an individual .java file. In the main method,(1) Create a Triangle object with default base and height values.(2) Create a Triangle object with specified base = 3 and height =4. TASK 3: Add a toString() method to the Triangle class. In this toString() method,(1) Print the base, height, and area of a Triangle object.(2) Call the toString() method of the superclass using the super key word.Then, in the main method of the TestTriangle class, make the two Triangle objects that youcreated in Task 2…arrow_forwardPlease solve this in java, using the Gui system(Jframe, Jpanel, etc) from java, not java fx thanks.arrow_forwardTask 4: Matplotlib Import the plotting function by the command: import matplotlib.pyplot as plt Plotting multiple lines Compute the x and y coordinates for points on sine and cosine curves and plot them on the same graph using matplotlib. Add x and y labels to the graph as well. Note: Please provide PYTHON (ANACONDA) code for above task.arrow_forward
- Why do we favor the event delegation model and its components when designing GUIs? What is your answer using the applicable examples?arrow_forwardPlease discuss the differences between bagging and boosting and give an applicationalexample for each (please choose a specific method, such as AdaBoost or XGBoost, whendiscussing the boosting examples)arrow_forwardUse the Eclipse IDE to write java code for Functionality for the “Doctor” interface: The system should allow a doctor to assign a new doctor to a patient using the list of all doctors. The system should then send confirmation messages to the patient and both doctors The appearance of the interface is not important as long as the required functionality is provided. That is, you are not expected to implement a fancy looking interface. just ensure it has a home button and a log out buttonarrow_forward
- Class definitions for DateTimerPicker and MonthCalender are provided below.arrow_forwardShow me a nice UI. Distinguish between GUIS, NUIS, and CLIs.arrow_forwardPlease add the code after this one. The code has to be in java eclipse. Please add comments in what you are doing. I'll appreciate it public class Computer { private String ModelNumber; private String BrandName; private String manufacturingDate; private int NumberOfCores; //Constructor a public Computer() {} //Construct a computer object with model, BrandName, NumberOfCoresComputer (String ModelNumber, String BrandName, String manufacturingDate, int NumberOfCores){ this.ModelNumber=ModelNumber; this.BrandName=BrandName; this.manufacturingDate=manufacturingDate; this.NumberOfCores=NumberOfCores;}//generate getters/setterspublic String getModel() { return ModelNumber;} public void setModel(String ModelNumber) { ModelNumber = ModelNumber;} public String getBrandName() { return BrandName;} public void setBrandName(String brandName) { BrandName = brandName;} public String getManufacturingDate() { return manufacturingDate;} public void setManufacturingDate(String…arrow_forward
- An int array stores the following values: 9 4 12 2 6 8 18 How many passes will it take for a selection sort to sort this array?arrow_forwardor this assignment, you will select either the Cat or the Dog Java class from the UML diagram. Open the Virtual Lab (Apporto) by clicking on the link in the Virtual Lab Access module. Then open your Eclipse IDE and create a new class. Use the Eclipse IDE Tutorial if you need help with creating a class in Eclipse. Before you begin, review the following UML Class Diagram, paying special attention to the attributes and behaviors of each class. As a note, though the diagram illustrates an inheritance relationship between the classes, the class you choose to implement does not have to inherit from the Pet class for the purposes of this assignment. You will learn more about implementing inheritance in later modules. Next, you will implement either the Cat or Dog Java class. Your class must meet all of the specifications from the UML Class diagram. Be sure to include the following in your Cat or Dog class: All attributes (variables) with appropriate data types. Note that the types are…arrow_forwardAssume the base package for an Eclipse project is edu.westga.cs1301.drinks and that you are writing tests for the dispense method of a DrinkMachine class. Use this information to answer the following questionWhat should you name your test class?arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education