
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
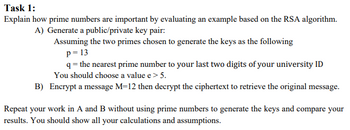
Transcribed Image Text:Task 1:
Explain how prime numbers are important by evaluating an example based on the RSA algorithm.
A) Generate a public/private key pair:
Assuming the two primes chosen to generate the keys as the following
p=13
q = the nearest prime number to your last two digits of your university ID
You should choose a value e > 5.
Encrypt a message M=12 then decrypt the ciphertext to retrieve the original message.
B)
Repeat your work in A and B without using prime numbers to generate the keys and compare your
results. You should show all your calculations and assumptions.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Given the plaintext “I LOVE CRYPTO”, what is the ciphertext given that: Row Transposition Cipher algorithm with the key is 3214.arrow_forwardSuppose you intercepted the following encrypted message: 20 5 21 3 49 4 49 3 4 15 You also know the encryption key is d=7 and it was determined using n=55. Decrypt this message. Assume that letters 'A' through 'Z' were initially coded using 1 through 26 and a blank was initially coded using 27. no hand wriitenarrow_forward1. Asymmetric Encryption and Message Authentication: a) The primitive root of a prime number is the basic principle of Diffie-Hellman. i) Is 3 the primitive root of 11? Show the proof with your calculation. ii) What are the important criteria for selecting a prime number in cryptography? Is 11 a good choice for such a purpose? b) Find the parameters stated using the Diffie-Hellman methods, given the user A and B shared a prime number and its primitive root of 23 and 5, respectively. i) If user A public key value is 8, find the A’s private key. ii) If user B public key value is 19, what is the common secret key? c) In the following scenario, we will compare the security services that are given by digital signatures (DS) and message authentication codes (MAC). We assume that James can read all messages send from Chan to Badrul and the other way around, too. James has no knowledge of any keys but the public one in the case of DS. State whether and…arrow_forward
- Assume Alice and Bob both have public and private keys in a public key setting. If Alice wants to send Bob a signed message, Alice first hashes her message and the hash using _'s key. decrypts/ Alice/ private encrypts/Alice/private decrypts/ Bob/ private encrypts/ Bob/publicarrow_forwardI need help with the following problems in cryptography. A. Encrypt the message “Freedom” using the Playfair matrix M F H I K U N O P Q Z V W X Y E L A R G D S T B C T B. Construct the Playfair matrix with the keyword “LARGEST” and encrypt the message “Freedom” again. C. Compare the results obtained in A and B. How do you account for these results?arrow_forwardExplain what the following lines of code do pad = len(byteblock)%16 * (-1)byteblock_trimmed = byteblock[64:pad]ciphertext = cipher.encrypt(byteblock_trimmed)ciphertext = byteblock[0:64] + ciphertext + byteblock[pad:]arrow_forward
- Write the solution in detail:A) Encrypt the following message using poly-alphabetic cipher:Plaintext: “HELLO WORLD”Key:Shift the first letter three positions to its rightShift the second letter five positions to its rightShift the third letter seven-position to its left B) Using the same key, decrypt the following text:Cipher text= “vjv xwb wd”arrow_forwardq8-arrow_forwardQuestion # 1: Use the Affine cipher method to encrypt the following plaintext:Summer Term CompletedKey pair (K1, K2) = (5, 3) Remember: i need a Mathematics solution not computer program You must show all the steps of your workarrow_forward
- how to do this; Given an RSA public and private key of (note that not all of the private key is given):N = 3065977e = 425d = 713237 Decrypt the following message that has been encrypted using the public key above: 1559791arrow_forwardDecode the number using the given private key. Decode the number M = 15 using the private key d = 53 and n = 77. Assume you are decoding the number using the RSA cryptosystem. Note: You can use the Modular Exponentiation calculator to help with the calculation. a 63 (mod 77), decoded number = 63 b 64 (mod 77), decoded number = 64 C 65 (mod 77), decoded number = 65 d. 66 (mod 77), decoded number = 66arrow_forwardSuppose your RSA public key is PK: {n, e} = {13861, 37}. Your friend sends you a ciphertext C = 9908. But unfortunately you have forgotten your private key, now you have to crack it yourself.a) Write down a possible condition of factors p and q.p= q=b) What is your private key SK: {d}?d=c) What is the plaintext of your friend’s message?The plaintext M =d) Suppose the plaintext M is a 12-digit number consisting of a prefix “19” and 1234567890. What is the corresponding ciphertext? Since M is greater than n, you only need to encrypt four digits at a time. Ignore redundant zeros. e.g., 0001 = 1. The result should contain three integers.The ciphertext C0 =arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education