
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
thumb_up100%
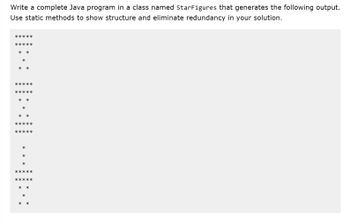
Transcribed Image Text:Write a complete Java program in a class named StarFigures that generates the following output.
Use static methods to show structure and eliminate redundancy in your solution.
*****
*****
* *
*
*
*
*****
* *
*
*
*****
*****
*
*
*
*****
*****
*
*
**
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- USING JAVA: Part A) Implement a superclass Appointment and subclasses Onetime, Daily, and Monthly. An Appointment has a description (for example, “See the dentist”) and a date. Write a method, occuresOn(int year, int month, int day) The check whether the appointment occurs on that date. For example, for appointment, you must check whether the day of the month matches. This fill an array of Appointment objects with a mixture of appointments. Have the user enter a date and print out all appointments that occur on that date. Part B) Improve the appointment book by giving the user the option to add new appointments. The user must specify the type of the appointment, the description, and the date.arrow_forwardIn Java code: Write the class encapsulating the concept of money, assuming that money has the following attributes: dollars, cents In addition to the constructors, the accessors and mutators, write the following methods: public Money() public Money(int dollars, int cents) public Money add(Money m) public Money substract(Money m) public Money multiply(int m) public static Money[] multiply(Money[] moneys, int amt) public boolean equals(Money money) public String toString() private void normalize() // normalize dollars and cents field Add additional helper methods if necessary. Use the following test driver program to test your Money class: public class MoneyTester{public static void main(String[] args){Money m1 = new Money(8, 75); // set dollars to 8 and cents to 75Money m2 = new Money(5, 80); // set dollars to 5 and cents to 80 MoneyMoney m3 = new Money(); // initialize dollars to 0 and cents to 0System.out.println("\tJane Doe " + "CIS35A Spring 2021 Lab 4"); // useyour…arrow_forwardusing java *two classes*arrow_forward
- Utilize Salary.java. The file contains a program that shows how a manager decides an employee’s salary. Two input values are read in: an employee’s current salary a rating of the employee’s performance // ************************************************************// Salary.java// ************************************************************import java.util.Scanner;import java.text.NumberFormat;public class Salary{ public static void main (String[] args) { double currentSalary; // employee's current salary double raise; // amount of the raise double newSalary; // new salary for the employee int rating; // performance rating Scanner scan = new Scanner(System.in); System.out.print ("Enter the current salary: "); currentSalary = scan.nextDouble(); System.out.print ("Enter the performance rating (3 is Excellent, 2 is Good, or 1 is Poor): "); rating = scan.nextInt(); // Enter the code here:…arrow_forwardpublic class utils { * Modify the method below. The method below, myMethod, will be called from a testing function in VPL. * write one line of Java code inside the method that adds one string * to another. It will look something like this: * Assume that 1. String theInput is 2. string mystring is ceorge неllo, пу nane is * we want to update mystring so that it is неllo, пу nane is Ceorge */ public static string mymethod(string theInput){ System.out.println("This method combines two strings."); Systen.out.println("we combined two strings to make mystring); return mystring;arrow_forwarda Java program that defines and uses 3 overloaded methods (the Java file nameshould be “MethodOverload.java” and all the 3 methods should have the same methodname max). The 3 method headers are given below with their definitions:• int max(int n1, int n2, int n3):o to return the maximum of the passed 3 integer arguments.• double max(double d1, double d2, double d3):o to return the maximum of the passed 3 double arguments with use ofMath.max() method—that is, do not use if or if-else statement incomparing the numbers to find the smaller/smallest numbers.• int max(int n):In the main method of the application, a loop with switch-statement inside is required fortesting the different method calls and you need to generate random numbers for the inputsas the arguments for the methods (except for die-rolling case where an input is enteredfrom the keyboard.). Specifically:• int max(int n1, int n2, int n3): the 3 random integers should be from the sequence2, 5, 8, 11, 14.• double max(double d1,…arrow_forward
- Write a program using java programing language. Write a Java class (called ShowNum) that displays the same number of asterisks (row and columns) as is input in 2 numbers. Your class should have a default constructor (number1 is 0, number2 is 0) and another constructor that inputs 2 numbers (integers). You'll need accessor methods for the numbers and a display method that displays as follows: Input: 2, 7 ******* ******* Demo the class in a client (called ShowNumClient) that allows the user to run the program as many times as they want (enter number and use display method). The user will signal with a sentinel (-1), when they want to terminate the client. Make sure that each number entered in the client is between 1 and 30.arrow_forwardCan you do it in Javaarrow_forwardjavaarrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education