
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
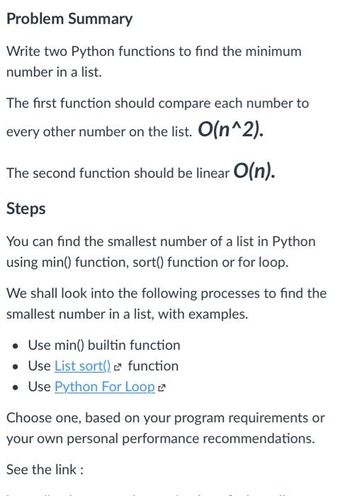
Transcribed Image Text:Problem Summary
Write two Python functions to find the minimum
number in a list.
The first function should compare each number to
every other number on the list. O(n^2).
The second function should be linear O(n).
Steps
You can find the smallest number of a list in Python
using min() function, sort() function or for loop.
We shall look into the following processes to find the
smallest number in a list, with examples.
Use min() builtin function
• Use List sort() function
• Use Python For Loop
Choose one, based on your program requirements or
your own personal performance recommendations.
See the link :
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Please I need it quickly !!! In python We have a list (named data) of numbers sorted in ascending order, for example: data = [2, 4, 5, 9, 10, 12, 13, 17, 18, 20] Write a function (named DataVar(data)), which take a list (data) as input parameter and performs the following steps on the list: 1) it finds the mean m of the data (for the given example, it is m = (2 + 4 + 5 + 9 + 10 + 12 + 13 + 17 + 18 + 20)/10 =110/10 = 11). 2) then, it finds the difference of data and m. Essentially, it finds for all data: Diff = data-m For the given example, Diff = [-9, -7, -6, -2, -1, 1, 2, 6, 7, 9]. 3) then, it finds the sum of Diff and 7. Essentially, it finds for all data: Sums = Diff+7 For the given example, Sums = [-2, 0, 1, 5, 6, 8, 9, 13, 14, 16]. 4) then, it finds the square of all the elements of Sums, such that Squares = square of the elements of Sums. For the given example, Squares = [4, 0, 1, 25, 36, 64, 81, 169, 196, 256]. 5) it finds the average of Squares and stores it in result, and…arrow_forwardWrite a function little_sum (number_list, limit) that returns the sum of only the numbers in number_list that are less than or equal to the given limit. In this question you must use a for loop and you are not allowed to use the sum function. For example: Test Result numbers = [1, 2, 3, 4, 5, 6] total = little_sum(numbers, 3) print(total) values = [6, 3, 4, 1, 5, 2] 10 total = little_sum(values, 4) print(total)arrow_forwardWrite a function count_evens(nums) that takes a list of ints called nums and returns the number of even ints in the given list. Note: the % "mod" operator computes the remainder, e.g. 5 % 2 is 1.arrow_forward
- for pythonarrow_forwardIn pythonWrite a function called compter_les_votes that accepts a list of ballots as input (of arbitrary length) and produces a report as a dictionary. The ballots have the form of a couple (valid, condidat) where candidate is the name of one of the candidates in the election, and valid is a boolean that indicates whether or not the ballot is valid. For example, for the following list of bulletins: [(True, 'Pierre'), (False, 'Jean'), (True, 'Pierre'), (True, 'Jacques')]Your function must return the following dictionary: { "number of ballots": 4, "invalid ballots": 1, "results": { "Stone": 2, "Jacques": 1 }}Note that you do not have to display the dictionary, only return it.arrow_forwardUse Python when answering the question: Write a function primeFac that computes the prime factorization of anumber: it accepts a single argument, an integer greater than 1 it returns a list containing the prime factorization each number in the list is a prime number greater than 1 the product of the numbers in the list is the original number the factors are listed in non-decreasing order Output is in the attached picture:arrow_forward
- In python We have a list (named data) of numbers sorted in ascending order, for example: data = [2, 4, 5, 9, 10, 12, 13, 17, 18, 20] Write a function (named DataVar(data)), which take a list (data) as input parameter and performs the following steps on the list: 1) it finds the mean m of the data (for the given example, it is m = (2 + 4 + 5 + 9 + 10 + 12 + 13 + 17 + 18 + 20)/10 =110/10 = 11). 2) then, it finds the difference of data and m. Essentially, it finds for all data: Diff = data-m For the given example, Diff = [-9, -7, -6, -2, -1, 1, 2, 6, 7, 9]. 3) then, it finds the sum of Diff and 7. Essentially, it finds for all data: Sums = Diff+7 For the given example, Sums = [-2, 0, 1, 5, 6, 8, 9, 13, 14, 16]. 4) then, it finds the square of all the elements of Sums, such that Squares = square of the elements of Sums. For the given example, Squares = [4, 0, 1, 25, 36, 64, 81, 169, 196, 256]. 5) it finds the average of Squares and stores it in result, and returns it. For the given…arrow_forwardPYTHON Complete the function below, which takes two arguments: data: a list of tweets search_words: a list of search phrases The function should, for each tweet in data, check whether that tweet uses any of the words in the list search_words. If it does, we keep the tweet. If it does not, we ignore the tweet. data = ['ZOOM earnings for Q1 are up 5%', 'Subscriptions at ZOOM have risen to all-time highs, boosting sales', "Got a new Mazda, ZOOM ZOOM Y'ALL!", 'I hate getting up at 8am FOR A STUPID ZOOM MEETING', 'ZOOM execs hint at a decline in earnings following a capital expansion program'] Hint: Consider the example_function below. It takes a list of numbers in numbers and keeps only those that appear in search_numbers. def example_function(numbers, search_numbers): keep = [] for number in numbers: if number in search_numbers(): keep.append(number) return keep def search_words(data, search_words):arrow_forwardCan you use Python programming language to to this question? Thanksarrow_forward
- Create a list L containing at least 10 values ranging from j to k. Using a for loop, code a function that will compute and display the following list: L_out[0] = L[0] L_out[i] = L[i] + L[i-1] if i is odd and i is not equal to 0 L_out[i] = L[i] * 3 if i is even and i is not equal to 0 where L[i] represents the value stored in L at the position i. Example: L ‘(2 3 4 5) L_out ‘(2 5 12 9)arrow_forwardWrite a function named "sort_word" that declares a parameter for a word and returns a string with the characters from the original word in sorted order. Hint: use the built-in Python sorted() function to convert the string into a sorted list of characters, and then use a for loop to convert the list back into a string. For example, given the word "tea", you would translate it into the String "aet". and return it. Write a function named "make_anagrams", that accepts a collection of unique words as a parameter and returns a dictionary. For each word in the collection: Call your "sort_word" function to obtain the sorted version of the word. Use the sorted word as the key in a dictionary. The value in the dictionary will be a list of any words that contain the exact same characters. To be clear: if you call your "sort_word" function with any word with the same characters in a different arrangement (e.g. "tea," "ate," or "eat"), you should receive the same key, and therefore store the…arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education