
Practice Problem 2.37 solution page 155
You are given the task of patching the vulnerability in the XDR code shown in the aside on page 100 for the case where both data types int and size_t are 32 bits. You decide to .eliminate the possibility of the multiplication overflowing by computing the number of bytes to allocate using data type unit64_t. You replace
In 2002, it was discovered that code supplied by Sun Microsystems to implement the XDR library, a widely used facility for sharing data structures between programs, had a security vulnerability arising from the fact that multiplication can overflow without any notice being given to the program.
Code similar to that containing the vulnerability is shown below:
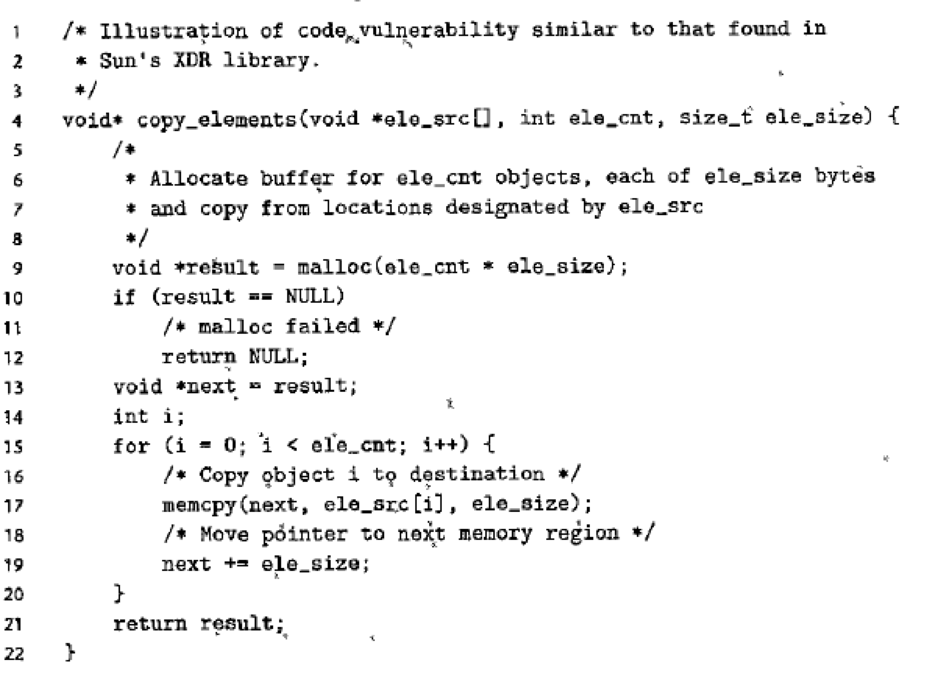
The function copy_elements is designed to copy ele_cnt data structures, each consisting of ele_ size bytes into a buffer allocated by the function on line 9. The number of bytes required is computed as ele_cnt * ele_size.
Imagine, however, that a malicious programmer calls this function with ele_cnt being 1,048,577 (220 + 1) and ele_size being 4,096 (212) with the program compiled for 32 bits. Then the multiplication on line 9 will overflow, causing only 4,096 bytes to be allocated, rather than the 4,294,971,392 bytes required to hold that much data. The loop starting at line 15 will attempt to copy all of those bytes, overrunning the end of the allocated buffer, and therefore corrupting other data structures. This could 1 cause the program to crash or otherwise misbehave.
The Sun code was used by almost every
A similar vulnerability existed in many implementations of the library function calloc. These have since been patched. Unfortunately, many-programmers call allocation functions, such as malloc using arithmetic expressions as arguments, without checking these expressions for overflow. Writing a reliable version of calloc is left as an exercise (Problem 2.76)
the original call to malloc (line 9) as follows:
Want to see the full answer?
Check out a sample textbook solution
Chapter 2 Solutions
COMPUTER SYSTEMS&MOD MSGT/ET SA AC PKG
Additional Engineering Textbook Solutions
Problem Solving with C++ (10th Edition)
Introduction to Programming Using Visual Basic (10th Edition)
Web Development and Design Foundations with HTML5 (8th Edition)
Digital Fundamentals (11th Edition)
Starting Out with C++: Early Objects
Artificial Intelligence: A Modern Approach
- Lo = Ro What is the result of applying the expansion box to R,? E(Ro) = What is the result of XORing the subkey with E(Ro)? ko O E(Ro) = We now apply the S-box transformation. S(ko Ð E(Ro)) = Finally we apply the permutation box to complete the function f. f(Ro) = P(S(ko Ð E(Ro))) = We can now compute the state of DES going into the next round. L = R1 =arrow_forwardProblem F. 73154. Trailing zeros Input file: Output file: Time limit: Memory limit: standard input standard output 1 second 256 megabytes In this problem, you are given 8-bit number r. Find the number of trailing zeros in its binary representation. Trailing zeros are the ones that we encounter until the first 1-bit if we traverse the binary representation from right to left. For example, the binary representation of the mumber 96 is 01100000. Number of 0-bits until the first 1-bit is 5 (considering that we traverse the binary representation from right to left). Input The first line of input contains a single number z – 8-bit number (1arrow_forwardWrite a function in MIPS assembly that copy the value of the 8th element of a word array to the 5th element. The starting address of the array is in $s0. Note thatthe index of the array starts with 0; i.e., the index of the 1st element in the array is 0. Please only modify $t0 in the code you write.arrow_forwardQ 2/A- Write a program to add the following five data bytes stored in data segment offset starting from [0800H], if the sum generates a carry , stop the adding ,and store (2B) in data segment offset [0440H], otherwise, continue adding and store the sum in data segment offset [0440H], Data (H): 04,06 ,01,02 and 11.arrow_forwardWrite a MIPS procedure that takes as its three parameters the starting address of an integer array, and two positive integers low and high, and returns the sum of the low’th through the high’th array elements. For example, for the array 3, 8, -1, 5, 4, 3, 9 and low and high values of 2 and 4, the return value should be 12 (since the sum of the 2nd through the 4th array elements is 8 + -1 + 5 = 12). Also, write a main program to test your procedure. Your main program should input the number of integers n in the array from the user (you may assume that n is at most 25), input the n integers, and then input the integers low and high. Your main program should then invoke your procedure, output the return value, and terminate. Your code must use the “standard” conventions for passing parameters and returning results.arrow_forwardM E su meleing... Problem 4 This problem is very similar to Problem 2. and you should use your solution to Problem 2 as starter code. The inputs are the same, but the output is a bit different: rather than telling the user how many slices in total will be left over, display the number of whole tiramisus plus number of slices from the tiramisu that had some slices removed. Sample Runs: nickemimi MINGW64 /c/Nick/CSULA/Cs2011/Code S java TiramisUAndPeoplez How many tiramisus? 5 How many slices per tiranisu? 4 How many people? 8 If you split ail tiranisus evenly among 8 people, you will have 1 full melting... nickamimi MINGW64 /c/Nick/CSULA/Cs2011/Code S java TiramisUandPeople2 HOW many tiramisus? 3 How many slices per tiramisu? 4 HOw many people? 7 If you split all tiramisus evenly among 7 people, you wi11 have 1 full ft over. melting... nickamini MINGW64 /c/Nick/CSULA/CS2011/Code S java TiramisUAndreoplez How many tiranisus? S HOW many slices per tiramisu? 5 HOW many people? 9 If you…arrow_forwardQ2/ Write a program to add the followig five data bytes stored in data segment offset starting from [0500H], if the sum generates a carry, stop the adding and store (01) in data segment offset [0600H], otherwise, continue adding and store the sum in data segment offset [0600H],arrow_forward6. Implement F (X,Y,Z) = XY'Z + YZ' by using a) Only one 4-to-1 MUX with X and Y as Select lines for MSB and LSB respectively. b) Only one 2-to-1 MUX with Z as select line.arrow_forwardQ1- Write a program in assembly language for the 8085 microprocessor to send one byte of data located at the memory address (3000H ) using SOD at a baud rate of 1200. Information: The 8085 processor operates at a frequency of 3.072 MHz . When sending the required byte, you must adhere to the following: The two high bits of the start bits(1 1) must be sent, after that the data bits are sent, after that the low bit of the stop bit (0) is sent. The following flowchart will help you. The solution must be integrated and include the calculation of the baudrate delay timearrow_forwardQ1- Write a program in assembly language for the 8085 microprocessor to send one byte of data located at the memory address (3000H) using SOD at a baud rate of 1200. Information: The 8085 processor operates at a frequency of 3.072 MHz. When sending the required byte, you must adhere to the following: The two high bits of the start bits must be sent, after that the data bits are sent, after that the low bit of the stop bit is sent. The following flowchart will help you. The solution must be integrated and include the calculation of the baud rate delay time Transmit Set up Character Bit Counter • Send Start Bit No Wait Bit Time Get Character in Accumulator Output Bit Using Do Wait Bit Time Rotate Next Bit in Do Decrement Bit Counter Is It Last Bit? Yes • Add Parity if Necessary Send Two Stop Bits Return (a)arrow_forwardFor the following code, explain what the register file and forwarding unit are doing during thefifth cycle of execution. If any comparisons are being made, mention them. Remember, usethe forwarding unit from class, not the book. LOOP:LDUR X1, [X6, #40]ADD X5, X5, X8ADD X6, X6, X8STUR X1, [X5, #20]CBZ X1, LOOParrow_forwardthis is COmputer machine architecture ! Help me fix the following code as theres an error. what were trying to accoplish; The assignment is to create a MIPS program that corrects bad data using Hamming codes. The program is to request the user to enter a 12-bit Hamming code and determine if it is correct or not. If correct, it is to display a message to that effect. If incorrect, it is to display a message saying it was incorrect and what the correct data is (the 12-bit Hamming code) again in hex. I will be testing only with single bit errors, so the program should be able to correct my tests just fine. You do not need to worry about multiple bit errors. # This program corrects bad data using Hamming codes # It requests the user to enter a 12-bit Hamming code and determines if it is correct or not # If correct, it displays a message to that effect. If incorrect, it displays a message # saying it was incorrect and what the correct data is (the 12-bit Hamming code) again in hex. # This…arrow_forwardarrow_back_iosSEE MORE QUESTIONSarrow_forward_ios
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education





