
Hidden tasks performed by DBMS when users update and retrieve data.
Explanation of Solution
A DBMS is of no use to any user if it's not capable of providing some functions. Updation and retrieval are the fundamental job of a DBMS. Thus, a DBMS must provide to its users the ability to perform same. These tasks are solely the responsibility of a DBMS and a user needs not be aware of them.
The general steps followed in almost all operations are in diagram below:
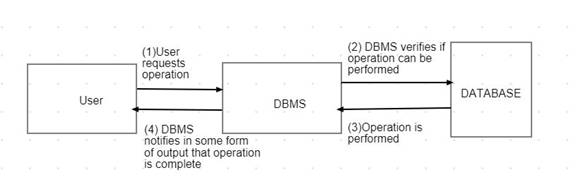
An operation contains instructions given by users and some tasks that are performed at the backend.
The difference usually occurs at step 2 and 3 where more than one sub operations might be needed to complete the task.
An updation operation can be performed by a user in the following way: by adding a new record, changing an existing records or it's deletion. All these consist of some instructions given by user and some task performed by DBMS.
Updation:
1. adding new records:
User enters an item and requests the DBMS to add a new item into database.
Following tasks are performed by DBMS following the request:
- It checks whether the records already exist in Database
- If not, it creates a new record and adds it to the database.
- Informs the user that the operation is complete, and the record is now a part of the database.
2. Changing a record:
User requests the DBMS to change an item from the database.
Following tasks are performed by DBMS following the request:
- It reads the data from database that needs to be changed.
- It displays the current data to user so that new value can be provided for changing.
- It changes the value as soon as new value is provided.
3. Deleting a record:
User requests the DBMS to delete an item from the database.
Following tasks are performed by DBMS following the request:
- It reads the data from database that needs to be deleted.
- It displays the current data to user so that user is able to see what will be deleted.
- It deletes the value as soon as user confirms the deletion action.
Retrieval:
A user is capable of reading a value from database. Following are the steps performed by DBMS to complete the operation:
- It finds and reads the record from database
- It displays the record to user
Thus, an operation consists of both the task done by a user and the tasks performed by a user. The DBMs is fully capable of performing these sub tasks at backend without the user being aware of it.
Want to see more full solutions like this?
Chapter 7 Solutions
EBK CONCEPTS OF DATABASE MANAGEMENT
- Identify different types of security approaches used by your organization, or other organization that you re familiar with, to secure any DBMSs that are accessible over the web. Present at least two different examples of the security approaches used.arrow_forwardData warehousing DBMs are evaluated using a set of specific criteria.arrow_forwardUsing default settings may either improve data integrity or harm it, depending on the situation.arrow_forward
- True or False: Mandatory security mechanisms of a DBMS can be set by the engineer implementing the database and include constraints to ensure data integrity such as: strict data types enforcing or requiring fields to be entered using lists to restrict data entry. Group of answer choicesarrow_forwardBriefly explain what is meant by referential integrity and how it is enforced bythe DBMSarrow_forwardExplain the principles of data recovery and fault tolerance in distributed DBMS, including techniques like shadow paging and logging.arrow_forward
 Enhanced Discovering Computers 2017 (Shelly Cashm...Computer ScienceISBN:9781305657458Author:Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. CampbellPublisher:Cengage Learning
Enhanced Discovering Computers 2017 (Shelly Cashm...Computer ScienceISBN:9781305657458Author:Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. CampbellPublisher:Cengage Learning
