
Computer Systems: A Programmer's Perspective (3rd Edition)
3rd Edition
ISBN: 9780134092669
Author: Bryant, Randal E. Bryant, David R. O'Hallaron, David R., Randal E.; O'Hallaron, Bryant/O'hallaron
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Textbook Question
Chapter 8, Problem 8.23HW
One of your colleagues is thinking of using signals to allow a parent process to count events that occur in a child process. The idea is to notify the parent each time an event occurs by sending it a signal and letting the parent's signal handler increment a global counter variable, which the parent can then inspect after the child has terminated. However, when he runs the test program in Figure 8.45 on his system, he discovers that when the parent calls printf, counter always has a value of 2, even though the child has sent five signals to the parent. Perplexed, he comes to you for help. Can you explain the bug?
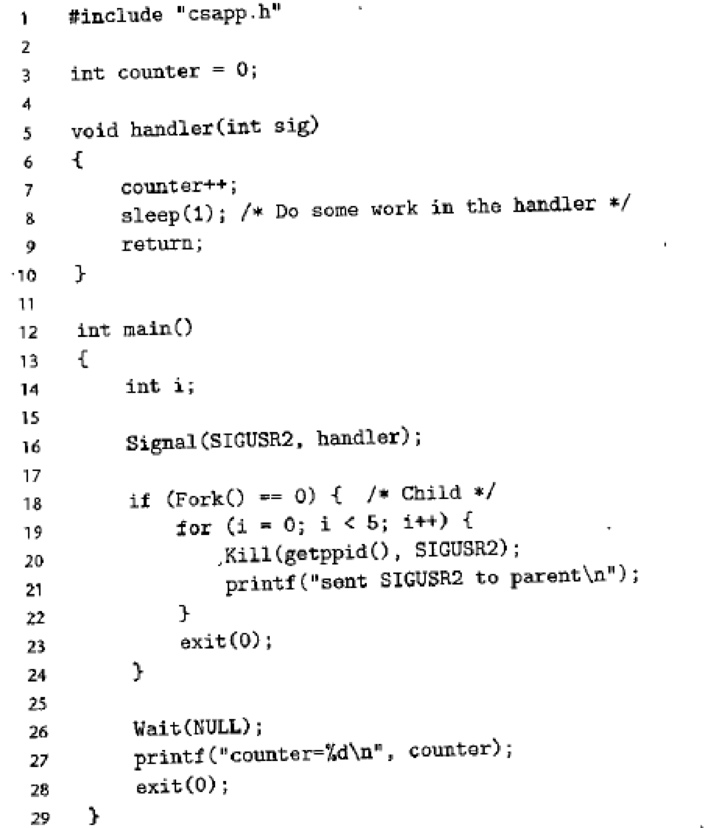
Figure 8.45 Counter program referenced in Problem 8-23.
Expert Solution & Answer
Want to see the full answer?
Check out a sample textbook solution
Students have asked these similar questions
Hi, how can i find out what the programm in phyton does without actually using phyton idle for it? :)
For example, in the task i was given i had to find out what the programm i sent in the picture prints without inserting the programm into phyton idle.
How long does an interruption typically last on average? What kind of effects does this have on switching contexts?
The Java Virtual Machine (and your computer’s assembly language) support a goto instruction so that the search can be “wired in’’ to machine code, like the program at right (which is exactly equivalent to simulating the DFA for the pattern as in KMPdfa, but likely to be much more efficient). To avoid checking whether the end of the text has been reached each time i is incremented, we assume that the pattern itself is stored at the end of the text as a sentinel, as the last M characters of the text. The goto labels in this code correspond precisely to the dfa[] array. Write a static method that takes a pattern as input and produces as output a straight-line program like this that searches for the pattern.
Straight-line substring search for A A B A A A
int i = -1;sm: i++;s0: if (txt[i]) != 'A' goto sm;s1: if (txt[i]) != 'A' goto s0;s2: if (txt[i]) != 'B' goto s0;s3: if (txt[i]) != 'A' goto s2;s4: if (txt[i]) != 'A' goto s0;s5: if (txt[i]) != 'A' goto s3; return i-8;
Chapter 8 Solutions
Computer Systems: A Programmer's Perspective (3rd Edition)
Ch. 8.2 - Prob. 8.1PPCh. 8.4 - Prob. 8.2PPCh. 8.4 - Prob. 8.3PPCh. 8.4 - Prob. 8.4PPCh. 8.4 - Practice Problem 8.5 (solution page 797) Write a...Ch. 8.4 - Practice Problem 8.6 (solution page 797) Write a...Ch. 8.5 - Practice Problem 8.7 (solution page 798) Write a...Ch. 8.5 - Prob. 8.8PPCh. 8 - Prob. 8.9HWCh. 8 - In this chapter, we have introduced some functions...
Ch. 8 - How many hello output lines does this program...Ch. 8 - How many "hello' output lines does this program...Ch. 8 - Prob. 8.13HWCh. 8 - How many hello output lines does this program...Ch. 8 - How many "hello lines does this program print?Ch. 8 - Prob. 8.16HWCh. 8 - Prob. 8.17HWCh. 8 - Consider the following program: Determine which of...Ch. 8 - How many lines of output does the following...Ch. 8 - Use execve to write a program called my1s whose...Ch. 8 - What are the possible output sequences from the...Ch. 8 - Write your own version of the Unix system function...Ch. 8 - One of your colleagues is thinking of using...Ch. 8 - Modify the program in Figure 8.18 so that the...Ch. 8 - Write a version of the fgets function, called...
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Do you know when the next interruption will occur? What does this have to do with switching contexts?arrow_forwardWrite the robot program using the VAL+ for the following automation case. First draw the problem; then handwrite the VAL+ code. The robot picks up FIVE blocks of size 100x100x100 mm that are stacked at a fixed position and place them at the corners and center of a square table of size 500 x 500 mm. Select the original position on the table on your own.arrow_forwardWhat is a semaphore? What is the difference between a binary semaphore and a countingsemaphore? Show that if the wait and signal operations in a semaphore are not executedatomically, then mutual exclusion may be violated.arrow_forward
- We speak of programs’ being “partially” correct and being “totally” correct. A program is totally correct just when it does what any reasonable person would expect from its specification: if started in a situation (“state” of the computer) where its pre-condition holds, then it eventually terminates in a case where its post condition has.Are these two partially and totally in terms of what they imply about the specification for the pre-condition and post-condition? If so, explain precisely what they mean in this regard. If not, explain what is different about what they imply.arrow_forwardAnswer the given question with a proper explanation and step-by-step solution. Write a LabVIEW program that executes an equivalent of the following C-like code, where x is an input and y is an output (Formula Nodes are not allowed): if(abs(x)< 0.1) y = 1; else if(x>=0) y = 0; else y = 2; Run your program for the following inputs: x = 0.05; -0.05; 1; and -1.arrow_forwardIs it possible for a single procedure to get blocked while it is being carried out? It is expected that your responses would be accompanied by logic.arrow_forward
- Could you assist me with question 2.7 part B? I'm finding this problem quite challenging and would appreciate help with creating a state diagram for the push-down automaton related to part B. I started the problem shown in the photo but I don't know why it is incorrect, can you use the photo that I used.question for 2.7 2.7 Give informal English descriptions of PDAs for the language. B. The complement of the language {a^n b^n | n ≥ 0}arrow_forwardIt is possible to represent human concepts (such as mathematics) in a programming language, so that we can get machines to obey specific rules. Because of this, a parser must convert OUR text and symbols into tokens. How come the machine doesn't simply do what we tell it to?arrow_forwardWrite a C++ Program to check whether a string is a palindrome or not. A palindrome is a word, verse, or sentence (such as " I ere I saw Elba") that reads the same backward or forward. In this task, the inserted string should consist of letters only (A to Z and a to z). In case of an invalid character is inserted, the output will be the phrase "Wrong entry". If the iserted string is palindrome, the output will be the word "Palindrome", else it will be "NOT Palindrome". The inserted string is case insensitive. IMPORTANT NOTE Do not add any cout statements except for the final answer as specified above. Do not add "Enter a number", "the number of digits is" or any similar prompts. Also note that the automatic grader is case-sensitive; so "palindrome" is wrong but "Palindrome" is right. Do not add any unnecessary spaces inside the strings of cout statements " ". You may add any libraries needed. I/O Program Input: A string consists of letters only Program Output: A phrase that shows…arrow_forward
- Two subroutines in a C# programme create a String object of a given size and a StringBuilder object of the same size, respectively. Utilizing objects from the Timing class that we created at the start of the book, each of the subroutines is timed. Three times are needed to complete this process: once for 100 characters, once for 1,000 characters, and once for 10,000 characters. The times are then given for each size in pairs.arrow_forwardAssume we are given the task to build a system that can distinguish junk e-mail. What is in a junk e-mail that lets us know that it is junk? How can the computer detect junk through a syntactic analysis? What would you like the computer to do if it detects a junk e-mail-delete it automatically, move it to a different file, or just highlight it on the screen?arrow_forwardImplement the counter increment, and branch back to the start of the loop. When you havecompleted these steps, the basic structure of the counter control loop has been implemented,and your code should look similar to the following:.text li $s0, 0 lw $s1, n start_loop: sle $t1, $s0, $s1 beqz $t1, end_loop # code block addi $s0, $s0, 1 b start_loop end_loop:.data n: .word 5arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education
Binary Numbers and Base Systems as Fast as Possible; Author: Techquikie;https://www.youtube.com/watch?v=LpuPe81bc2w;License: Standard YouTube License, CC-BY
Binary Number System; Author: Neso Academy;https://www.youtube.com/watch?v=w7ZLvYAi6pY;License: Standard Youtube License