
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Perform Dijkstra’s algorithm (while (Q is not empty){...}, where Q is
a min priority queue) on the following graph for source node “s”, writing out
every execution of the RELAX function, the update to the priority queue and the
updates of distance from the source node and parent for the currently visited node.
a min priority queue) on the following graph for source node “s”, writing out
every execution of the RELAX function, the update to the priority queue and the
updates of distance from the source node and parent for the currently visited node.
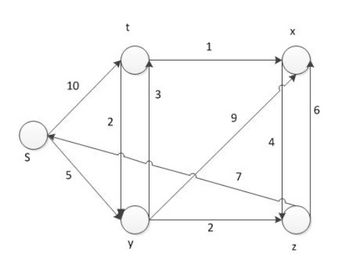
Transcribed Image Text:S
10
5
2
t
y
3
1
2
9
7
★
N
6
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 4 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Explain the difference of A* algorithm from Dijkstra’s algorithmusing pseudo-code for the RELAX function (i.e. how the estimate of the distancefrom the source node is updated). Explain the meaning of variables in thatfunction.arrow_forwardComputer Networks The book demonstrated that a poisoned reverse will prevent the count-to-infinity problem caused when there is a loop involving three directly connected nodes. However, other loops are possible. Will the poisoned reverse solve the general case count-to-infinity problem encountered by Bellman-Ford? Yes, the poisoned reverse will prevent a node from offering a path that includes preceding nodes in the loop. It will not, preceding nodes may still be used in the computation of the distance vector offered by a given node.arrow_forward1 6 0 2 4 7 3 5 Graph Garrow_forward
- The book demonstrated that a poisoned reverse will prevent the count-to-infinity problem caused when there is a loop involving three directly connected nodes. However, other loops are possible. Will the poisoned reverse solve the general case count-to-infinity problem encountered by Bellman-Ford? -Yes, the poisoned reverse will prevent a node from offering a path that includes preceding nodes in the loop. -It will not, preceeding nodes may still be used in the computation of the distance vector offered by a given node.arrow_forwarda.Given the steps of Kruskal’s algorithm, analyze each loop and find its running time cost in terms of V and E. MST-KRUSKAL(G,w) A ← for each vertex v V MAKE-SET(v) sort E into non-decreasing order by w for each (u, v) taken from the sorted list if FIND-SET(u) FIND-SET(v) then A ← A {(u, v)} UNION(u, v) return A b. What is the total asymptotic running time of Kruskal’s algorithmarrow_forwardProve that a minimum spanning tree of a graph component must include a shortest edge. It is possible, in Dijkstra’s algorithm, that an edge removed from the priority queue is not useful: it takes us to a previously visited node. Some of these extraneous edges can be avoided by not placing an edge in the priority queue if the destination has already been visited. Is it still possible to encounter an edge to a previously visited node?arrow_forward
- Problem 3. Given a node in a binary search tree, its successor is the successor node in the sorted order determined by an inorder tree traversal. Use pseudo codes to write a function BST-Successor, which returns the successor node of a given node in a BST. You may assume that all the BST regular operation functions are existed and can be used for your function.arrow_forwardLet T : P −→ L be a function that inputs a perfect binary tree and outputs a list of vertices, defined as follows. B. If X is a binary tree consisting only of a single vertex v, then T (X ) = v, a list with only one entry. R. If X is a binary tree with root v, left subtree Xl and right subtree Xr , then T (X ) equals the list T (Xl ), T (Xr ), v.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education