
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Answer the given question with a proper explanation and step-by-step solution.
i only want java statement please read the question carefully
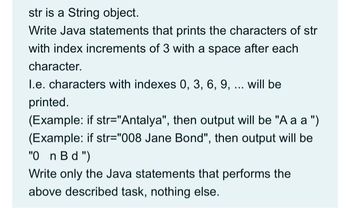
Transcribed Image Text:str is a String object.
Write Java statements that prints the characters of str
with index increments of 3 with a space after each
character.
I.e. characters with indexes 0, 3, 6, 9, ... will be
printed.
(Example: if str="Antalya", then output will be "Aaa")
(Example: if str="008 Jane Bond", then output will be
"0_n Bd")
Write only the Java statements that performs the
above described task, nothing else.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Write Java code pleasearrow_forwardDetermine whether a string is a palindromeA palindrome is a string of characters that reads the same from right to left as it does from left to right, regardless of punctuation and spaces.The specifications for this assignment are: •Write and test a non-recursive solution in Java that determines whether a string is a palindrome •Your program should consist of at least two methods: (1) the main method (2) the method which performs the task of determining whether the specified string is a palindrome. You should name this method isPalindrome. You should name the class that contains your “main” method and the isPalindrome method FindPalindrome. •You must use a Stack and a Queue in your solution: Write your own Stack and Queue based on the Vector in the Java API and use those in your solution. You should name those classes StackVector and QueueVector respectively. You already have access to the relevant exception classes and interfaces for the above ADTs. •All of your belong to a Java…arrow_forwardWriting a Modular Program in Java Summary In this lab, you add the input and output statements to a partially completed Java program. When completed, the user should be able to enter a year, a month, and a day to determine if the date is valid. Valid years are those that are greater than 0, valid months include the values 1 through 12, and valid days include the values 1 through 31. Instructions Notice that variables have been declared for you. Write the simulated housekeeping() method that contains input statements to retrieve a year, a month, and a day from the user. Add statements to the simulated housekeeping()method that convert the String representation of the year, month, and day to ints. Include the output statements in the simulated endOfJob()method. The format of the output is as follows:month/day/year is a valid date. or month/day/year is an invalid date. Execute the program entering the following date: month = 5, day = 32, year =2014Observe the output of this…arrow_forward
- write a code in java (using recursion)arrow_forwardUsing the Python language answer the following questions below. Please tell me what program you use if it is IDLE or Atom or a python website please provide the website you use.arrow_forwardPlease answer question. This is pertaining to Java programming language 2-17arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education