
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
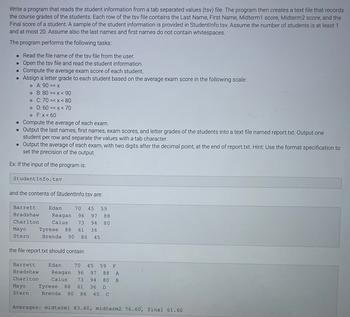
Transcribed Image Text:Write a program that reads the student information from a tab separated values (tsv) file. The program then creates a text file that records
the course grades of the students. Each row of the tsv file contains the Last Name, First Name, Midterm1 score, Midterm2 score, and the
Final score of a student. A sample of the student information is provided in StudentInfo.tsv. Assume the number of students is at least 1
and at most 20. Assume also the last names and first names do not contain whitespaces.
The program performs the following tasks:
. Read the file name of the tsv file from the user.
• Open the tsv file and read the student information.
• Compute the average exam score of each student.
• Assign a letter grade to each student based on the average exam score in the following scale:
。 A: 90=<x
o F:x < 60
• Compute the average of each exam.
• Output the last names, first names, exam scores, and letter grades of the students into a text file named report.txt. Output one
student per row and separate the values with a tab character.
• Output the average of each exam, with two digits after the decimal point, at the end of report.txt. Hint: Use the format specification to
set the precision of the output.
Ex: If the input of the program is:
o B: 80 =< x < 90
o
C: 70 =< x < 80
o
D: 60 =< x < 70
Student Info.tsv
and the contents of StudentInfo.tsv are:
Barrett Edan 70 45 59
Bradshaw Reagan 96 97 88
Charlton
73 94 80
Caius
Tyrese 88 61 36
Brenda 90 86 45
Mayo
Stern
the file report.txt should contain:
Barrett
Bradshaw
Charlton
Mayo
Stern
Edan 70 45 59 F
Reagan 96 97 88 A
Caius 73 94 80 B
Tyrese 88 61 36 D
Brenda 90 86 45 C
Averages: midterm1 83.40, midterm2 76.60', final 61.60
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Given a text file containing the availability of food items, write a program that reads the information from the text file and outputs the available food items. The program first reads the name of the text file from the user. The program then reads the text file, stores the information into four separate arrays, and outputs the available food items in the following format: name (category) -- description Assume the text file contains the category, name, description, and availability of at least one food item, separated by a tab character. Ex: If the input of the program is: food.txt and the contents of food.txt are: Sandwiches Ham sandwich Classic ham sandwich Available Sandwiches Chicken salad sandwich Chicken salad sandwich Not available Sandwiches Cheeseburger Classic cheeseburger Not available Salads Caesar salad Chunks of romaine heart lettuce dressed with lemon juice Available Salads Asian salad Mixed greens with ginger dressing, sprinkled with sesame Not available Drinks Water…arrow_forwardIn C++ Query the user for the name of a file. Open and process that file, reporting the number of words in the file and the number of words containing each letter, and the length of that word. Assume that any word exceeding nine characters is counted as a ten character word. If the same letter appears more than once, it is counted only once. The result should be a matrix of 26 rows (one row for each letter) and ten columns (one column for each word length (1-10), and the contents of the matrix must be displayed. As an example, assume the file contains only two words - “rotten” and “egg”. When processing “rotten”, rows for r, o, t, e and n would have the contents of column 6 incremented because “rotten” is a six letter word. When processing “egg”, rows for e and g would have the contents of column 3 incremented because “egg” is a three letter word.arrow_forwardC++ Write a program that reads the student information from a tab separated values (tsv) file. The program then creates a text file that records the course grades of the students. Each row of the tsv file contains the Last Name, First Name, Midterm1 score, Midterm2 score, and the Final score of a student. A sample of the student information is provided in StudentInfo.tsv. Assume the number of students is at least 1 and at most 20. Assume also the last names and first names do not contain whitespaces. The program performs the following tasks: Read the file name of the tsv file from the user. Open the tsv file and read the student information. Compute the average exam score of each student. Assign a letter grade to each student based on the average exam score in the following scale: A: 90 =< x B: 80 =< x < 90 C: 70 =< x < 80 D: 60 =< x < 70 F: x < 60 Compute the average of each exam. Output the last names, first names, exam scores, and letter grades of the…arrow_forward
- >> classicVinyls.cpp For the following program, you will use the text file called “vinyls.txt” attached to this assignment. The file stores information about a collection of classic vinyls. The records in the file are like the ones on the following sample: Led_Zeppelin Led_Zeppelin 1969 1000.00 The_Prettiest_Star David_Bowie 1973 2000.00 Speedway Elvis_Presley 1968 5000.00 Spirit_in_the_Night Bruce_Springsteen 1973 5000.00 … Write a declaration for a structure named vinylRec that is to be used to store the records for the classic collection system. The fields in the record should include a title (string), an artist (string), the yearReleased (int), and an estimatedPrice(double). Create the following…arrow_forwardwrite in c++Write a program that would allow the user to interact with a part of the IMDB movie database. Each movie has a unique ID, name, release date, and user rating. You're given a file containing this information (see movies.txt in "Additional files" section). The first 4 rows of this file correspond to the first movie, then after an empty line 4 rows contain information about the second movie and so forth. Format of these fields: ID is an integer Name is a string that can contain spaces Release date is a string in yyyy/mm/dd format Rating is a fractional number The number of movies is not provided and does not need to be computed. But the file can't contain more than 100 movies. Then, it should offer the user a menu with the following options: Display movies sorted by id Display movies sorted by release date, then rating Lookup a release date given a name Lookup a movie by id Quit the Program The program should perform the selected operation and then re-display the menu. For…arrow_forwardLoad the airline JSON file into a python dictionary, save it to a text file and print the airlines that operated in Boston and SanFrancisco airports during the month of June.arrow_forward
- In pythonarrow_forwardWrite a program that reads movie data from a CSV (comma separated values) file and output the data in a formatted table. The program first reads the name of the CSV file from the user. The program then reads the CSV file and outputs the contents according to the following requirements: Each row contains the title, rating, and all showtimes of a unique movie. A space is placed before and after each vertical separator ('|') in each row. Column 1 displays the movie titles and is left justified with a minimum of 44 characters. If the movie title has more than 44 characters, output the first 44 characters only. Column 2 displays the movie ratings and is right justified with a minimum of 5 characters. Column 3 displays all the showtimes of the same movie, separated by a space. Each row of the CSV file contains the showtime, title, and rating of a movie. Assume data of the same movie are grouped in consecutive rows. Hints: Use the find() function to find the index of a comma in each row of…arrow_forwardIn pythonarrow_forward
- Write a Pandas program to calculate the total of the examination attempts and the mean score in data frame.Display the first four rows in the output. import pandas as pdimport numpy as npexam_data = {'name': ['Anastasia', 'Dima', 'Katherine', 'James', 'Emily', 'Michael', 'Matthew', 'Laura', 'Kevin', 'Jonas'], 'score': [12.5, 9, 16.5, np.nan, 9, 20, 14.5, np.nan, 8, 19], 'attempts': [1, 3, 2, 3, 2, 3, 1, 1, 2, 1], 'qualify': ['yes', 'no', 'yes', 'no', 'no', 'yes', 'yes', 'no', 'no', 'yes']}labels = ['a', 'b', 'c', 'd', 'e', 'f', 'g', 'h', 'i', 'j'] df = #TO DO -- Complete the Code# print(df)print("\nSum of the examination attempts by the students:")print(sum,"\n") #TO DO -- Complete the Codeprint("\nMean score for each different student in data frame:")print(np.mean(cleanedlist)) #TO DO -- Complete the Codeprint() #TO DO -- Complete the Code Intended ouput: Sum of the examination attempts by the students:19 Mean score for each different student in data…arrow_forwardI am looking to write two python programs for golf data. The Westminster Amateur Golf Club has a tournament every weekend. The club president has askedyou to design and write two programs. The first program will read each player's name and golf score as keyboard input, and then save(append) these records in a file named golf.dat (Each record will have a field for the player'sname and a field for the player's score, separated by commas). The second program will read the records from the golf.dat file and displays them. n addition, italso displays the name of the player with the best (lowest) score. The output should look like this: Program 1Enter a player's name: Larry FineEnter the player's score: 20Do you want to enter another record?Enter y for yes or anything else for no: y Enter a player's name: Moe HowardEnter the player's score: 21Do you want to enter another record?Enter y for yes or anything else for no: y Enter a player's name: Curly HowardEnter the player's score: 22Do you…arrow_forwardThis project involves generating a boarding pass ticket and storing it in a file. The application should take the passenger details as input. The details of the boarding pass are to be stored in a file. The details should include valid data such as: name, email, phone number, gender, age, boarding pass number, date, origin, destination, estimated time of arrival (ETA), departure time. The application should generate a boarding pass ticket using the boarding pass details. The generated ticket should contain the following information: Boarding Pass Number, Date, Origin, Destination, Estimated time of arrival (ETA), Departure Time Name, Email, Phone Number, Gender, Age Total Ticket Price The user will be required to enter their Name, Email, Phone Number, Gender, Age, Date, Destination, and Departure Time into the console or GUI. From the input the computer must generate the ETA and Ticket Price. The computer must generate the boarding pass number ensuring the number is unique. All…arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education