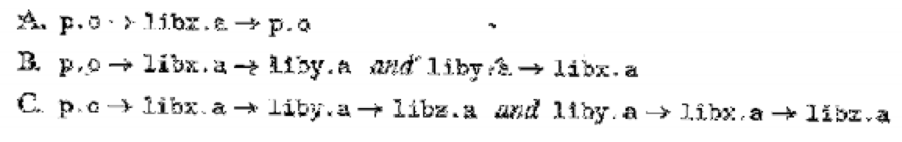
Let a and b denote object modules or static libraries in the current directory, and let a →b denote that a depends on b, in the sense that b defines a symbol that is referenced by a For each of the following scenarios, show the minimal command line (i.e., one with the least number of object file and library arguments) that will allow the static linker to resolve all symbol references:
Want to see the full answer?
Check out a sample textbook solution
Chapter 7 Solutions
Computer Systems: A Programmer's Perspective Plus Mastering Engineering With Pearson Etext -- Access Card Package (3rd Edition)
Additional Engineering Textbook Solutions
Java How to Program, Early Objects (11th Edition) (Deitel: How to Program)
Java How To Program (Early Objects)
Introduction to Java Programming and Data Structures, Comprehensive Version (11th Edition)
Starting Out with Java: From Control Structures through Data Structures (3rd Edition)
Objects First with Java: A Practical Introduction Using BlueJ (6th Edition)
- Write a test client TestBinarySearch.java for use in testing the implementations of min(), max(), floor(), ceiling(), select(), rank(),deleteMin(), deleteMax(), and keys() that are given in the text. Start with the standard indexing client . Add code to take additional command-line arguments, as appropriatearrow_forwardShow a skeleton/template of how to protect a library's interface file from being included multiple times. (Your answer should work for all cases -- not just simple ones.)arrow_forwardWhy must the symbol/name used in C++'s inclusion guard on a library interface file be unique? (Hint: A good technique to use here is proof by contradiction -- assume that the symbol needn't be unique and show what happens when two libraries to be #include'd in the same program share the same symbol.)arrow_forward
- Develop a java program to define an Symbol table class so that each symbol is associated with a numeric value. The two main methods are set() and get(): void set(String sym, int value); int get(String sym); The set() method associates the int value with the symbol sym, while the get() method performs the complement of retrieving the int value previously associated Define appropriate exceptions so that clients of the Symbol table may respond to conditions appropriately. For example, when they retrieve the value of a nonexist clients can either stop execution and display an error message or use a default value of 0 Symbol Numeric Valuearrow_forwardWhen using a C++ inclusion guard on a library interface file, why is it essential that the symbol or name used in the guard not be identical to any other uses of the symbol or name in the guard? Assuming that the symbol does not need to be unique and then showing what occurs when two libraries that are to be #included in the same application share the same symbol is an effective use of the proof by contradiction technique in this circumstance. Here, we have an actual application.arrow_forwardConsider the implementation of the data structure stack. If we create an integer stack then the push and pop operations will handle only integer elements. If we create a character stack then the push and pop operations will handle only character type elements. But creating so many copies of implementation makes the code complex to maintain. Hence the principle of genericity is used and a template class can be created. This container class can handle any data type element at run time.In the same contrast explain the importance of modeling in object oriented programming. Plagiarized answer will be given thumbsdown.arrow_forward
- Implement a generic priority queue in Java and test it with an abstract Cryptid class and two concrete Cryptid classes, Yeti and Bigfoot. Create a code package called pq and put all the code for this assignment in it. Write the abstract class Cryptid. A Cryptid has a name (a String) and a public abstract void attack() method. Name should be protected. The class implements Comparable<Cryptid>. The compareTo method returns a negative int if the instance Cryptid's name (that is, the name of the Cryptid you called the method on) is earlier in lexicographic order than the name of the other Cryptid (the one passed in as an argument; it returns a positive int if the other Cryptid's name is earlier in lex order, and returns 0 if they are equal (that is, if they have all the same characters.) This part is easy; just have the method call String's compareTo() method on the instance Cryptid's name, with the other Cryptid's name as the argument, and return the result. Extend Cryptid…arrow_forwardGiven the linked list data structure, implement a sub-class TSortedList that makes sure that elements are inserted and maintained in an ascending order in the list. So, given the input sequence {1,7,3,11,5}, when printing the list after inserting the last element it should print like 1, 3, 5, 7, 11. Note that with inheritance, you have to only care about the insertion situation as deletion should still be handled by the parent class.arrow_forward3. Consider a hospital information system using which patients can take appointment with a doctor on first come first serve basis and their appointments are maintained in a queue. a. Discuss by giving reasons on which of the following data structures is most suitable for implementing such appointment queue, when considering that there is no limit on how many patients a doctor can see in any given day. *One dimensional array Linked list b. Write and execute a java program to create an object of class appointment queue, and perform operations such as insert, remove, and display. Give your reflection on each of these operationarrow_forward
- What happened? When libvector.a is processed, U is empty, so nomember object files from libvector.a are added to E.arrow_forwardConsider the Person class in Problem 1. Implement the interface PersonPriorityQueueInterface provided in the assignment. In your implementation, you must use an instance of AList (which you used in Problem 1) to store the list of persons. We consider that a person whose age is higher than a second person also has a higher priority. Thus, the method peek(), for example, should return the person who is the oldest in the list. Your implementation should be O(n) for add, and O(1) for the remaining methods. Consider the Person class in Problem 1. Implement the interface PersonPriorityQueueInterface provided in the assignment. In your implementation, you must use an instance of AList (which you used in Problem 1) to store the list of persons. We consider that a person whose age is higher than a second person also has a higher priority. Thus, the method peek(), for example, should return the person who is the oldest in the list. Your implementation should be O(n) for add, and O(1)…arrow_forwardWrite a Java program using OOP concept that perform the union and symmetric difference between two sets. Use class, object and method in code. A = { a, b, c, e, f }B = { d, e, f, g }arrow_forward
 C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning
