
Computer Systems: A Programmer's Perspective (3rd Edition)
3rd Edition
ISBN: 9780134092997
Author: Bryant
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Concept explainers
Textbook Question
Chapter 8, Problem 8.24HW
Modify the
- 1. Each child terminates abnormally after attempting to write to a location in the read-only text segment.
- 2. The parent prints output that is identical (except for the PIDs) to the following:
child 12255 terminated by signal·11: Segmentation fault
child 12254 terminated by signal·11: Segmentation fault
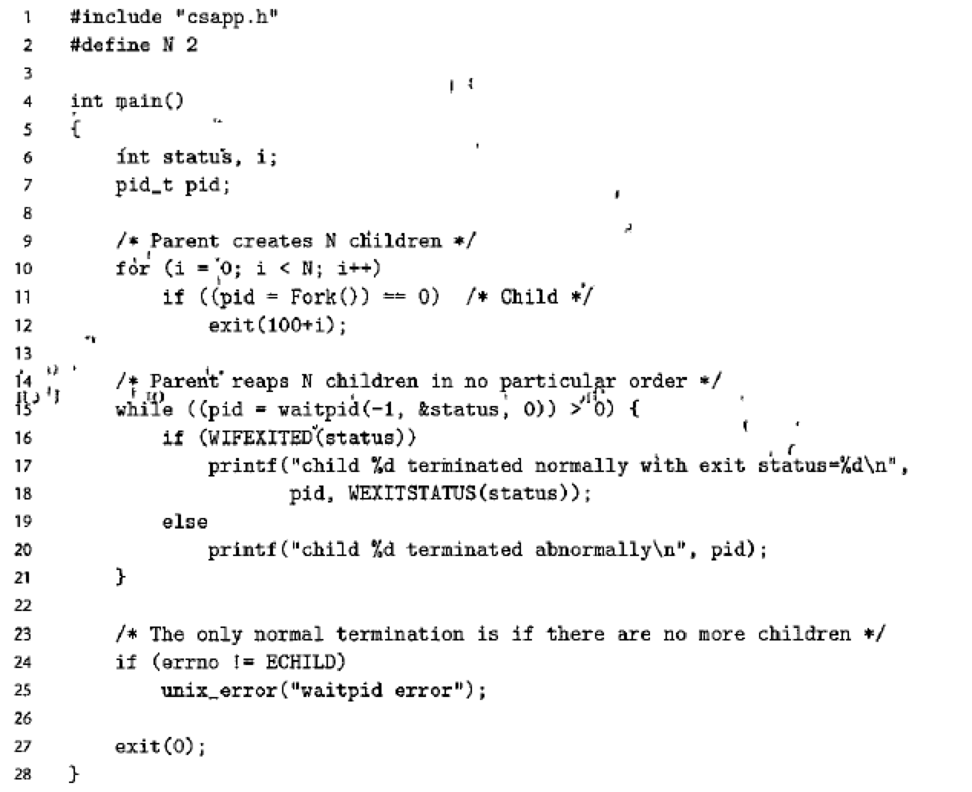
Figure 8.18 Using the waitpid function to reap zombie children in no particular order.
Expert Solution & Answer
Want to see the full answer?
Check out a sample textbook solution
Students have asked these similar questions
Consider the following snippets of code. Then, identify and describe thesorting algorithm used.num scores[5] = 90,85,65,95,75sort()x = 1while x < SIZEtemp = scores[x]y = x – 1while y >= 0 AND scores[y]>tempscores[y+1] = scores[y]y = y – 1endwhilescores[y+1] = tempx = x + 1endwhilereturn
Use C, C++, python or matlab to develop a program whose main routine accepts two parameters n and k, i.e. when you invoke your program from the shell, you pass it two parameters, n and k, where n >=16 and k >=3 and is in powers of 2 (e.g. 2, 4, 8, 16, etc.). Your main routine shall generate a random page trace of size n, where the page numbers have values ranging from 0 to ? − 1.
Develop a subroutine within your program that implements the LRU page replacement algorithm (as a separate function within your program). Your algorithm shall use the doubly linked list stack implementation as outlined in slide 29 of lecture 10). The function shall accept a page trace and a parameter f for the number of frames allocated.
Your main routine shall then apply the random page trace to the subroutine implementing the page replacement algorithm, multiple times (using only one trace, randomly generated), passing a parameter f (number of page frames used) that ranges from 4 to k. Your main…
Program to Implement Tower of Hanoi
Create function hanoi that takes the number of disks n and the names of the source, auxiliary and target pegs as arguments.
The base case is when the number of disks is 1, in which case simply move the one disk from source to target and return.
Move n – 1 disks from source peg to auxiliary peg using the target peg as the auxiliary.
Move the one remaining disk on the source to the target.
Move the n – 1 disks on the auxiliary peg to the target peg using the source peg as the auxiliary.
Case 1:Enter number of disks: 4Move disk 1 from peg A to peg B.Move disk 2 from peg A to peg C.Move disk 1 from peg B to peg C.Move disk 3 from peg A to peg B.Move disk 1 from peg C to peg A.Move disk 2 from peg C to peg B.Move disk 1 from peg A to peg B.Move disk 4 from peg A to peg C.Move disk 1 from peg B to peg C.Move disk 2 from peg B to peg A.Move disk 1 from peg C to peg A.Move disk 3 from peg B to peg C.Move disk 1 from peg A to peg B.Move disk 2 from peg A…
Chapter 8 Solutions
Computer Systems: A Programmer's Perspective (3rd Edition)
Ch. 8.2 - Prob. 8.1PPCh. 8.4 - Prob. 8.2PPCh. 8.4 - Prob. 8.3PPCh. 8.4 - Prob. 8.4PPCh. 8.4 - Practice Problem 8.5 (solution page 797) Write a...Ch. 8.4 - Practice Problem 8.6 (solution page 797) Write a...Ch. 8.5 - Practice Problem 8.7 (solution page 798) Write a...Ch. 8.5 - Prob. 8.8PPCh. 8 - Prob. 8.9HWCh. 8 - In this chapter, we have introduced some functions...
Ch. 8 - How many hello output lines does this program...Ch. 8 - How many "hello' output lines does this program...Ch. 8 - Prob. 8.13HWCh. 8 - How many hello output lines does this program...Ch. 8 - How many "hello lines does this program print?Ch. 8 - Prob. 8.16HWCh. 8 - Prob. 8.17HWCh. 8 - Consider the following program: Determine which of...Ch. 8 - How many lines of output does the following...Ch. 8 - Use execve to write a program called my1s whose...Ch. 8 - What are the possible output sequences from the...Ch. 8 - Write your own version of the Unix system function...Ch. 8 - One of your colleagues is thinking of using...Ch. 8 - Modify the program in Figure 8.18 so that the...Ch. 8 - Write a version of the fgets function, called...
Additional Engineering Textbook Solutions
Find more solutions based on key concepts
Write a program that reads a persons name in the following format: first name, then middle name or initial, and...
Problem Solving with C++ (9th Edition)
What is the main advantage of parallel transfer over serial transfer of binary data?
Digital Fundamentals (11th Edition)
Can RandomAccessFi1e streams read and write a data file created by DataOutputStream? Can RandomAccessFile strea...
Introduction to Java Programming and Data Structures, Comprehensive Version (11th Edition)
Which of the following are nor valid println statements? (Indicate all that apply.) a. System.out.println + Hel...
Starting Out with Java: From Control Structures through Objects (7th Edition) (What's New in Computer Science)
Programmers must be careful not to make syntax errors when writing pseudocode programs.
Starting Out with Programming Logic and Design (5th Edition) (What's New in Computer Science)
Why might doctors and nutritionists be interested in a device like DietSensor?
Using MIS (10th Edition)
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Suppose we have one floating-point multiplication unit in our microprocessor, and it takes seven cycles for it to complete the multiplication. If we get 3 back-to-back floating-point multiply instructions with no data dependency on the previous values, then what type of Hazard can we run into? a. Exception or Interrups b. Control Hazard c. No Hazard, as there is no dependency on the data between the three instructions e. Data Hazard f. Structural Hazardarrow_forwardModiflow y the beprogram given to include response time program;FCFS CPU SCHEDULING ALGORITHM #include<stdio.h>#include<conio.h>main(){int bt[20], wt[20], tat[20], i, n; float wtavg, tatavg;clrscr();printf("\nEnter the number of processes -- "); scanf("%d", &n); for(i=0;i<n;i++){printf("\nEnter Burst Time for Process %d -- ", i); scanf("%d", &bt[i]);}wt[0] = wtavg = 0; tat[0] = tatavg = bt[0]; for(i=1;i<n;i++){wt[i] = wt[i-1] +bt[i-1];tat[i] = tat[i-1] +bt[i]; wtavg = wtavg + wt[i]; tatavg = tatavg + tat[i];}printf("\t PROCESS \tBURST TIME \t WAITING TIME\t TURNAROUND TIME\n");for(i=0;i<n;i++){printf("\n\t P%d \t\t %d \t\t %d \t\t %d", i, bt[i], wt[i], tat[i]);}printf("\nAverage Waiting Time -- %f", wtavg/n);printf("\nAverage Turnaround Time -- %f", tatavg/n); getch();}arrow_forwardModiflow y the beprogram given to include response time program;FCFS CPU SCHEDULING ALGORITHM #include<stdio.h>#include<conio.h>main(){int bt[20], wt[20], tat[20], i, n; float wtavg, tatavg;clrscr();printf("\nEnter the number of processes -- "); scanf("%d", &n);for(i=0;i<n;i++){printf("\nEnter Burst Time for Process %d -- ", i); scanf("%d", &bt[i]);}wt[0] = wtavg = 0; tat[0] = tatavg = bt[0];for(i=1;i<n;i++){wt[i] = wt[i-1] +bt[i-1];tat[i] = tat[i-1] +bt[i]; wtavg = wtavg + wt[i]; tatavg = tatavg + tat[i];}printf("\t PROCESS \tBURST TIME \t WAITING TIME\t TURNAROUND TIME\n");for(i=0;i<n;i++){printf("\n\t P%d \t\t %d \t\t %d \t\t %d", i, bt[i], wt[i], tat[i]);}printf("\nAverage Waiting Time -- %f", wtavg/n);printf("\nAverage Turnaround Time -- %f", tatavg/n); getch();}arrow_forward
- The Java Virtual Machine (and your computer’s assembly language) support a goto instruction so that the search can be “wired in’’ to machine code, like the program at right (which is exactly equivalent to simulating the DFA for the pattern as in KMPdfa, but likely to be much more efficient). To avoid checking whether the end of the text has been reached each time i is incremented, we assume that the pattern itself is stored at the end of the text as a sentinel, as the last M characters of the text. The goto labels in this code correspond precisely to the dfa[] array. Write a static method that takes a pattern as input and produces as output a straight-line program like this that searches for the pattern. Straight-line substring search for A A B A A A int i = -1;sm: i++;s0: if (txt[i]) != 'A' goto sm;s1: if (txt[i]) != 'A' goto s0;s2: if (txt[i]) != 'B' goto s0;s3: if (txt[i]) != 'A' goto s2;s4: if (txt[i]) != 'A' goto s0;s5: if (txt[i]) != 'A' goto s3; return i-8;arrow_forwardSuppose you have a finite state machine that accepts bit strings divisible by 11. The FSM has 11 states R0, R1, ... , R10, each corresponding to the remainder when dividing by 11. Input is fed to the FSM one bit at a time from left to right, the same way we did in our in-class examples. If the machine is currently in state R7, an input of 1 should transition it to which state? Type the subscript only of the new state. Your answer should be an integer between 0 and 10, inclusive.arrow_forwardConvert this code to bash script to simulate producer-consumer problem using semaphores. #include<stdio.h>int mutex=1,full=0,empty=3,x=0;main(){ int n; void producer(); void consumer(); int wait(int); int signal(int); printf(“\n 1.Producer \n 2.Consumer \n 3.Exit”); while(1) { printf(“\n Enter your choice:”); scanf(“%d”,&n); switch(n) { case 1: if((mutex==1)&&(empty!=0)) producer(); else printf(“Buffer is full”); break; case 2: if((mutex==1)&&(full!=0)) consumer(); else printf(“Buffer is empty”); break; case 3: exit(0); break; } }}int wait(int s){ return (--s);}int signal(int s){ return(++s);}void producer(){ mutex=wait(mutex); full=signal(full); empty=wait(empty); x++; printf(“\n Producer produces the item %d”,x); mutex=signal(mutex);}void consumer(){…arrow_forward
- Consider a system with four page frames and a program that uses eight pages. Consider the reference string 0 1 7 2 0 3 1 7 0 1 7 and assume that all four page frames are initially empty. Consider the three following algorithms: a. Optimal page replacement b. FIFO page replacement c. LRU page replacement In each cases show a diagram (ASCII art recommended) that shows which pages are in which frames throughout time, and page faults at the bottom. For instance: would mean that at step 1 page 0 is referenced and loaded into frame 0, which is a page fault; then page 1 is referenced, and so on. The goal is to fill this table to see what in memory when and thus infer the number of page faults. The first 4 steps are ALWAYS the same, as above (i.e., just fill the four frames, with one page fault each time)arrow_forwardAssume a program core consisting of five conditional branches. The program corewill be executed millions of times. Below are the outcomes of each branch for oneexecution of the program core (T for taken and N for not taken).Branch 1: T-T-T-T-TBranch 2: N-N-NBranch 3: T-N-T-N-T-N-T-NBranch 4: T-T-T-N-N-NBranch 5: T-T-T-N-T-T-T-N-TAssume that behaviour of each branch remains the same for each program coreexecution. For dynamic branch prediction schemes, assume that each branch has its own prediction buffer and each buffer is initialized to the same state before eachexecution. List the predictions and the accuracies for each of the following branchprediction schemes:i) Always taken ii) Always not taken iii) 1-bit predictor, initialized to predicttaken iv) 2-bit predictor, initialized to weakly predict takenarrow_forwardConsider a system with four page frames and a program that uses eight pages. Consider the reference string 0 1 7 2 0 3 1 7 0 1 7 and assume that all four page frames are initially empty. Consider the three following algorithms: a. Optimal page replacement In each cases show a diagram (ASCII art recommended) that shows which pages are in which frames throughout time, and page faults at the bottom. For instance: The first 4 steps is ALWAYS the same (i.e., just fill the four frames, with one page fault each time)arrow_forward
- Use C, C++, python or matlab to develop a program whose main routine accepts two parameters n and k, i.e. when you invoke your program from the shell, you pass it two parameters, n and k, where n >=16 and k >=8and is in powers of 2 (e.g. 8, 16, 32, etc.). Your main routine shall generate a random page trace of length n, where the page numbers have values ranging from 0 to ? − 1. Develop a subroutine within your program that implements the FIFO page replacement algorithm (as a separate function within your program). The function shall accept a page trace and a parameter f for the number of frames allocated. Your main routine shall then apply the random page trace to the subroutine implementing the page replacement algorithm, multiple times (using only one trace, randomly generated), passing a parameter f (number of page frames used) that ranges from 4 to k. Your main routine shall then record the number of page faults for each run (i.e. for each f).Run your program using a page…arrow_forward) Consider the following sequence of virtual memory references (in decimal) generatedby a single program in a pure paging system:100, 110, 1400, 1700, 703, 3090, 1850, 2405, 2460, 4304, 4580, 3640a. Derive the corresponding reference string of pages (i.e. the pages the virtual addressesare located on), assuming a page size of 1024 bytes. (Assume that page numberingstarts at 0)b. For the page sequence derived above, determine the number of page faults for each ofthe following page replacement strategies, assuming that two (2) page frames areavailable to the program.i. LRUii. FIFOiii. OPT (Optimal)arrow_forwardThe following problem illustrates the way memory aliasing cancause unexpected program behavior. Consider the followingprocedure to swap two values:1 /* Swap value x at xp with value y at yp */2 void swap(long *xp, long *yp)3 {4 *xp = *xp + *yp; /* x+y */5 *yp = *xp - *yp; /* x+y-y = x */6 *xp = *xp - *yp; /* x+y-x = y */7 }If this procedure is called with xp equal to yp , what effect will ithave?A second optimization blocker is due to function calls. As an example,consider the following two procedures:1 long f();23 long func1() {4 return f ()+ f ()+ f ()+ f () ;5 }67 long func2() {8 return 4*f();9 }It might seem at first that both compute the same result, but withfunc2 calling f only once, whereas func1 calls it four times. It istempting to generate code in the style of func2 when given func1 asthe source.Consider, however, the following code for f:1 long counter = 0;23 long f() {4 return counter++;5 }This function has a side effect—it modifies some part of the globalprogram state.…arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education
Computational Software for Intelligent System Design; Author: Cadence Design Systems;https://www.youtube.com/watch?v=dLXZ6bM--j0;License: Standard Youtube License